Summary: Domain hijacking is the silent takeover of your digital identity. Discover how attacks happen, their impact, and best practices for preventing them.
Domain names represent brands and their reputation, and are valuable targets for attackers. When a domain is hijacked, threat actors gain control of your digital identity and may sell it on the dark web or use it to launch sophisticated phishing attacks.
Many victims remain unaware that they are the victims of identity theft until their web traffic drops or customers report phishing emails originating from their own brand. In this guide, we’ll break down what domain hijacking is and how it differs from DNS hijacking. We’ll also discuss the risks of losing your digital identity and how to protect it with the industry’s best practices.
Key takeaways
Domain hijacking, or domain theft, is the hostile takeover of your web identity by manipulating registrar records without the original owner’s permission.
Vulnerabilities, such as a lack of two-factor authentication or a reused password, create a low entry point for domain hijacking attacks.
A successful hijack allows attackers to redirect web traffic to malicious clones, intercept sensitive corporate emails, and destroy a brand’s reputation in minutes.
Threat actors usually take over the domain at the registrar level by using social engineering, credential harvesting, or exploiting compromised admin email accounts.
To prevent domain hijacking, businesses should use registry locks, two-factor authentication, and continuous monitoring of their external attack surface.
What is domain hijacking? The silent takeover of your digital infrastructure.
Domain hijacking happens when an unauthorized party takes control over a domain’s registration records. It gives attackers access to the entire ecosystem linked to that domain—from corporate email to cloud storage services and SaaS applications.
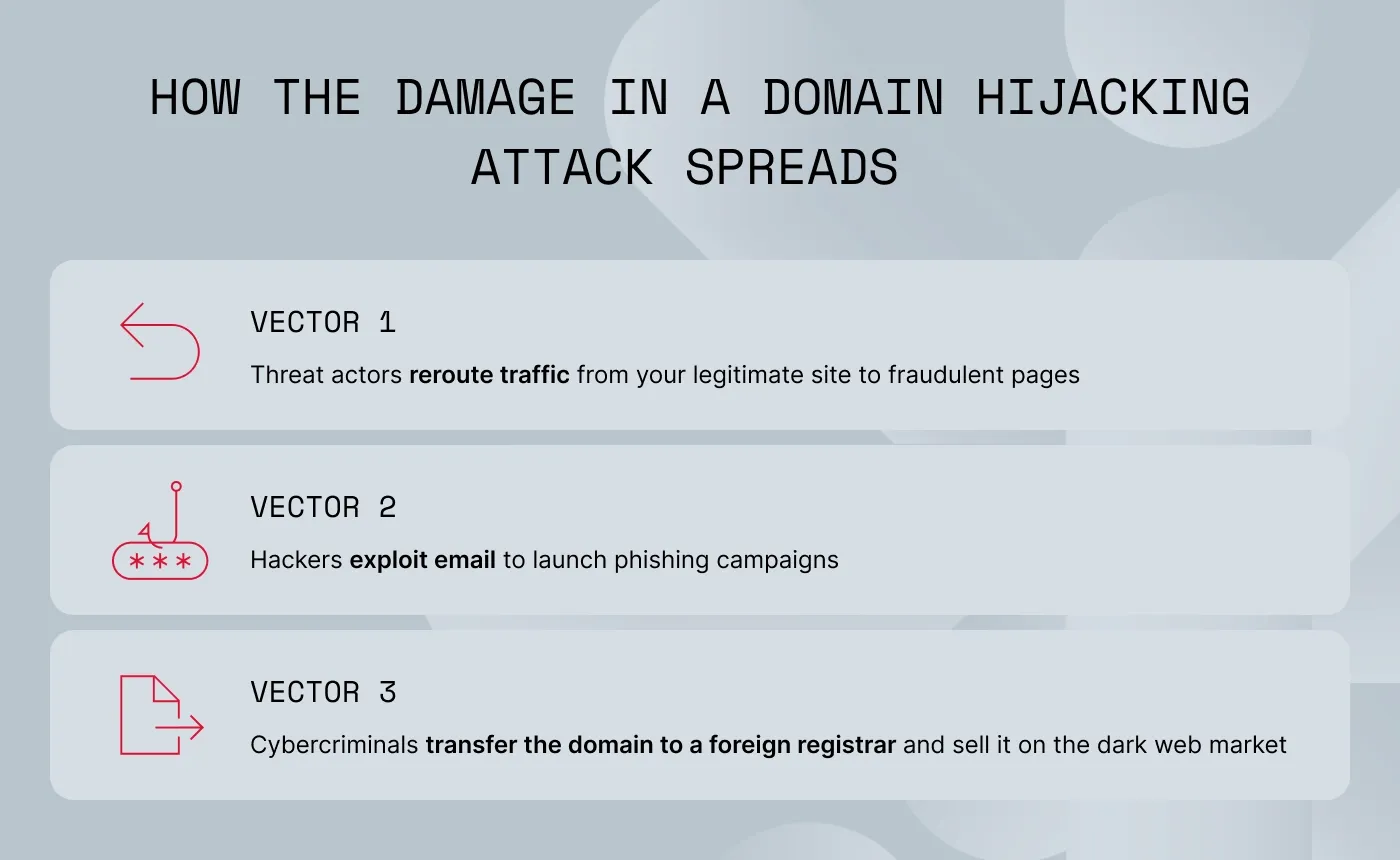
This takeover usually occurs “silently,” either by exploiting credential vulnerabilities or by using sophisticated phishing attacks to bypass security measures. Once in control, the damage spreads across these 3 vectors:
Rerouting traffic. Threat actors can redirect visitors from your legitimate site to fraudulent pages designed to steal customer data or distribute malware.
Exploiting email. By controlling your email exchanger (MX) records, hijackers use your domain to launch high-trust phishing campaigns to destroy your brand reputation and cause global providers to blacklist your organization.
Permanent domain loss. In the worst-case scenario, cybercriminals may transfer your domain to a foreign registrar and sell it on the dark web market, leaving you unable to recover your digital identity.
Understanding the distinction: domain hijacking vs. DNS hijacking
While both domain hijacking and DNS hijacking are equally damaging, they exploit different aspects of your online infrastructure. Understanding this distinction is key to protecting your company’s assets and brand reputation.
| | DNS hijacking/poisoning/spoofing |
|---|
| The domain account and legal ownership records. | The DNS server or settings that resolve names to IP addresses. |
| Total. Attackers can change the hijacked domain ownership, contact emails, and transfer the domain. | Partial/temporary. Attackers reroute traffic, but the owner still “owns” the domain. |
| Permanent unless legally reclaimed through a grueling recovery process. | Usually temporary until the DNS cache is cleared or settings are restored. |
| Loss of email, domain ownership, and all associated assets. | Intercepted traffic and man-in-the-middle data theft. |
Why is a hijacked domain a critical business risk?
Because domain name hijacking is a direct assault on a company’s financial integrity and legal standing, not merely a technical glitch, the consequences include:
Data exfiltration. Attackers use man-in-the-middle (MitM) setups to intercept live traffic, allowing them to harvest customer credentials, credit card details, or proprietary corporate data in real time.
The loss of customer trust. Once customers see your domain hosting fraudulent content, they may leave, which can result in a permanent loss of lifetime value.
SEO blacklisting and brand damage. If a hijacked domain is used to distribute phishing links or malware, search engines and security vendors will quickly blacklist the URL, destroying years of organic search authority and marketing investment.
Operational downtime. Reclaiming a stolen domain is a legal and administrative challenge that often involves grueling negotiations with registrars and registries and may take months to resolve.
High recovery costs. Organizations face massive expenses related to forensic investigations, legal fees, and the cost of rebuilding a compromised digital infrastructure.
The compliance and regulatory fallout. Domain hijacking can trigger an immediate failure of GDPR, SOC2, or HIPAA compliance, as it signals a total loss of control over data processing.
The mechanics of a takeover: how domain hijacking attacks happen
The goal of an attacker is to find the path of least resistance. They always target the weakest link in the chain, which may be an unpatched server, a vulnerable third-party provider, or a distracted employee.
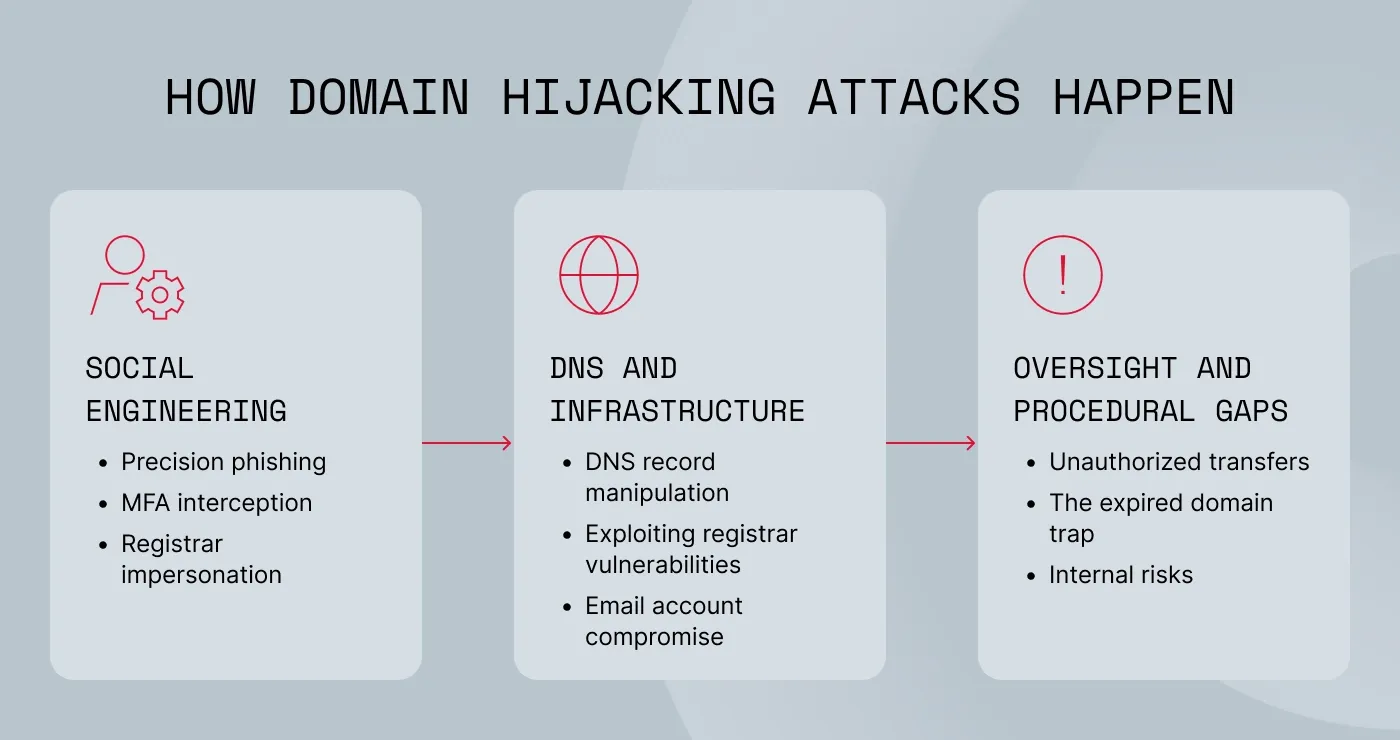
To better understand how these breaches happen, we can group their methods into 3 primary categories:
#1 The human element: deception and social engineering
Cybercriminals use psychological tricks like phishing and social engineering to get past security measures.
Precision phishing. Threat actors masquerade as domain registrars, using urgent “account suspension” warnings to lure admins to fraudulent login pages.
Multi-factor authentication (MFA) interception. Through attacker-in-the-middle proxies or SIM swapping, criminals can now bypass multi-factor authentication, capturing one-time codes in real time.
Registrar impersonation. Some attackers forgo technical hacks entirely, using social engineering instead to convince registrar support staff that they are the rightful owners who have simply “lost access.”
#2 Technical exploitation: DNS and infrastructure
Beyond manual social engineering, threat actors use technical vulnerabilities to seize control of a brand’s digital presence.
DNS record manipulation (DNS hijacking). By gaining access to a DNS host, cybercriminals can reroute web traffic and email to malicious destinations without ever changing the actual ownership of the domain.
Exploiting registrar vulnerabilities. Hijackers often target the registrars themselves, seeking out platforms with weak verification protocols or unpatched security flaws to execute a “silent takeover.”
Email account compromise. Once an attacker gets into the admin email inbox, they can trigger password resets and lock the legitimate owners out of every linked service.
#3 Oversight and procedural gaps
Negligence is often as dangerous as malice.
Unauthorized transfers. If a domain lacks a “transfer lock,” attackers may submit a change request, banking on the hope that a busy IT department will fail to notice the notification.
The expired domain trap. If a domain expires, bad actors can immediately re-register it to harvest returning traffic or impersonate the former brand.
Internal risks. Whether through intentional malice or an accident, insiders with high-level access remain a persistent threat to domain integrity.
The anatomy of an attack
Regardless of the method, the domain hijacker’s playbook follows a predictable sequence:
Infiltration. Entry is gained via phishing, social engineering, or technical exploit.
Consolidation. The attacker moves quickly to change passwords, DNS settings, and registrar details to solidify their hold.
Exploitation. The hijacked domain is used to redirect traffic, harvest data, or be held for ransom.
Once control is lost, every system tied to that domain—from corporate email to customer-facing websites—becomes an instrument for the attacker.
Related articles

Agnė SrėbaliūtėFeb 25, 20268 min read

Rūta TamošaitytėDec 16, 20256 min read
Signs your domain has been hijacked
So, how can you tell that your domain has been taken over? Well, the signs are not always visible on your homepage. Let’s look at some red flags that suggest your domain has been compromised:
Unexpected administrative alerts. The most direct sign is receiving notifications from your registrar about a domain transfer initiation, a password change, or an update to your contact information that you did not authorize.
Security warnings and traffic drops. You should be concerned if users report SSL/TLS certificate warnings, such as “Your connection is not private,” or if you experience a sudden, unexplained drop in website traffic. These could be signs that an attacker has rerouted your domain.
DNS and WHOIS anomalies. Unauthorized changes to your MX records (which handle email), A records (which point to your website), or CNAME records are clear indicators of a breach. Similarly, check if your WHOIS information—the public record of ownership—has been altered.
Email communication failures. If your outgoing emails are suddenly bounced back or failing DKIM/SPF authentication checks, it often means a hijacker has tampered with your mail server settings to send spam or intercept your messages.
Identifying these signs requires knowing what “normal” looks like for your systems.
How can you prevent domain hijacking? Your essential security checklist.
Protection from domain hijacking starts with choosing a reputable domain registrar that provides robust security.
Here are 6 practical steps for IT teams:
Enable two-factor authentication (2FA) on your domain registrar account. You can also move on beyond 2FA to FIDO2/WebAuthn keys for registrar logins for an extra layer of security.
Activate a relevant domain registry lock, a feature that requires manual authentication and explicit owner consent before any transfer or record change can be processed by the registrar.
Reduce the registrar sprawl by migrating all domains from fragmented personal or minor accounts into a single, enterprise-grade registrar with centralized oversight.
Enforce the principle of least privilege by regularly auditing all user accounts that have access to your registrar and removing any that are not essential.
Enable WHOIS privacy protection. Mask your domain registration details in the publicly accessible WHOIS database. By displaying registrar contact info instead of your own, you prevent attackers from gathering the intelligence needed for social engineering or identity theft.
Strengthen your human firewall. Educating staff and admins on how to recognize sophisticated phishing threats improves your domain’s overall security.
Domain monitoring as the core of attack surface management
Threat actors can now exploit misconfigurations in minutes, and that’s why manual point-in-time audits are no longer a viable defense strategy for the modern enterprise.
Beyond point-in-time audits. Manual checks are static and leave your infrastructure vulnerable between audit cycles. In a dynamic environment, you need a solution, like attack surface management (ASM), that provides continuous monitoring of your domain weekly or on demand, not every quarter.
Real-time automated alerts for any domain changes.
ASM identifies unauthorized changes as they happen. For example, if an MX record is altered or a registry lock is disabled, an automated system can trigger an incident response before a “silent” hijack is finalized.
Shadow IT discovery. ASM scans the internet to find domains and subdomains associated with your brand that you may have forgotten about, ensuring your digital perimeter has no unmonitored backdoors.
How NordStellar protects your business from domain hijacking
With rapid exploits and an expanded attack surface, you need continuous visibility to secure your business. NordStellar’s Attack Surface Management observes domain health every second:
Automatically maps your entire domain infrastructure, together with forgotten subdomains and cloud assets.
Detects misconfigurations, like those used in Sitting Ducks attacks, and unauthorized changes that could signal a hijacking attempt.
Adds an extra security layer that prevents domain-related blind spots before they are exploited.
Secure your digital identity now. Gain full visibility into your attack surface and stop domain hijackers before they strike. Try NordStellar for free.

Joanna Krysińska
Senior Copywriter
Joanna's family has a history in math and engineering, and she loves explaining complicated technical ideas. She helps people understand how hackers think and how to stay ahead of them by concentrating on the human side of cybersecurity.