Summary: Dread is a Reddit-like dark web forum for discussing topics that range from ransomware and cyberattack coordination to human rights and online privacy.
Dread is a dark web forum that was created as a central hub for underground communication after major marketplaces were seized and clear web bans were enacted. Often described as the “Reddit of the dark web,” it operates within the anonymity of the Tor network.
For cybersecurity analysts, understanding how Dread works is critical because it serves as a barometer of how threat actors discuss dark web markets and how they coordinate attacks.
Key takeaways
Dread is a Reddit-like dark web discussion forum that can be accessed via the Tor network.
The platform is used by cybercriminals, security analysts, journalists, and privacy advocates.
This dark web forum has a “subdread” structure and relies on PGP encryption for identity verification.
The topics discussed vary from dark web markets and ransomware to illicit trade, cybersecurity, and online privacy.
Security teams monitor Dread for early signs of data breaches, ransomware announcements, and new cyber threats.
What is the Dread forum?
Dread is a dark web discussion forum with a Reddit-like structure. It serves as a communication hub for cybercriminals, privacy advocates, and security researchers. Accessible only via the Tor network, Dread allows users to post and discuss topics ranging from ransomware and dark web markets to online privacy and human rights anonymously.
Access to the platform requires the encrypted Tor network, which prevents IP tracking. While Dread is notorious for hosting illegal discussions, such as tutorials on how to launch a ransomware attack, the forum also has “innocent” sub-communities where you can discuss video games or human rights issues in authoritarian regimes.
History and access
Created in 2018 by an administrator known as HugBunter, Dread was intended as a “free-speech” alternative for members of several darknet market communities who had been banned from Reddit. During the collapse of major darknet entities, including the shutdown of Dream Market and the various successors to AlphaBay, the forum served as the primary communication hub.
How the Dread forum works
Dread operates without JavaScript to reduce the risk of browser-based deanonymization.
Dread’s structure
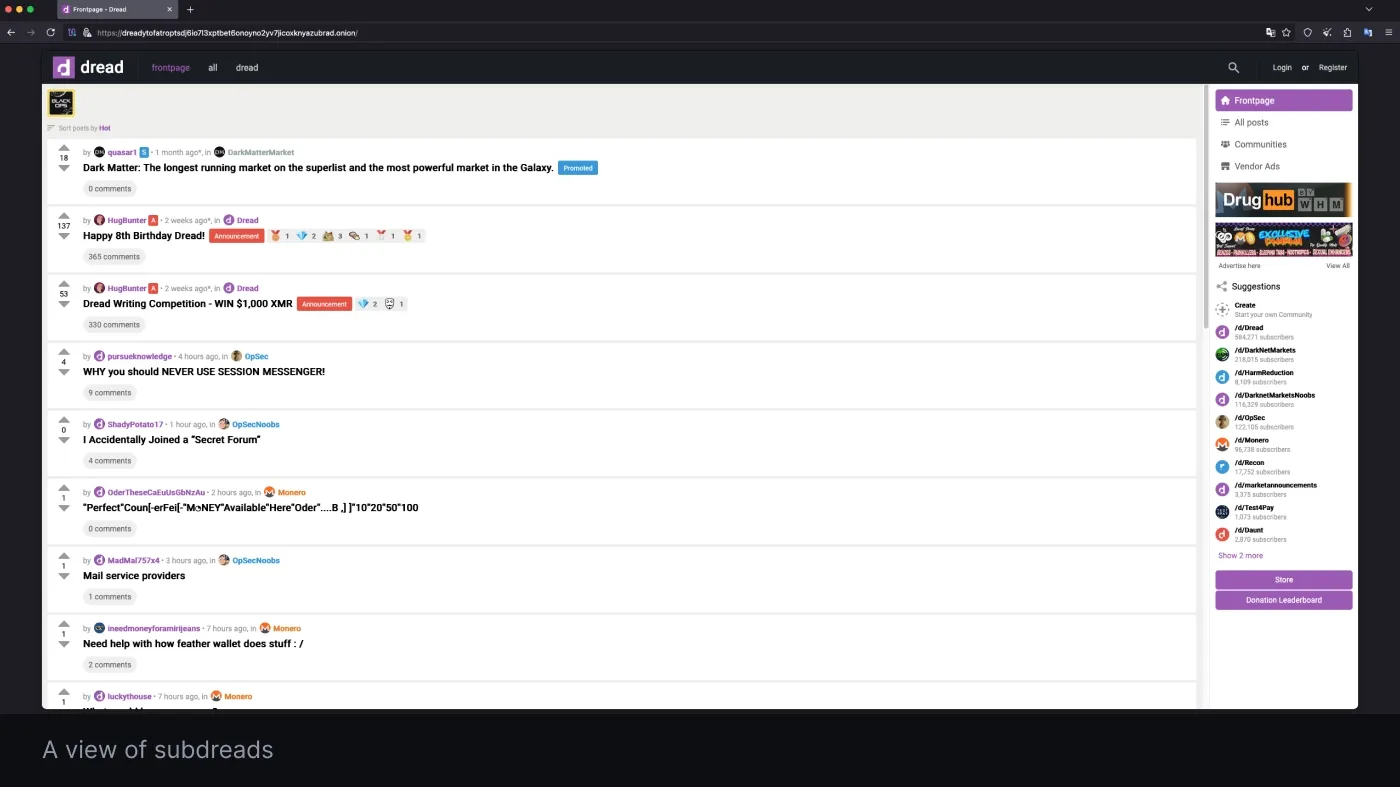
Upon account creation on Dread, new users can curate their feeds by selecting from a range of topics, including programming, cryptocurrency, and, alarmingly, ransomware and fraud.
The platform mimics Reddit’s user interface and has a clear structure:
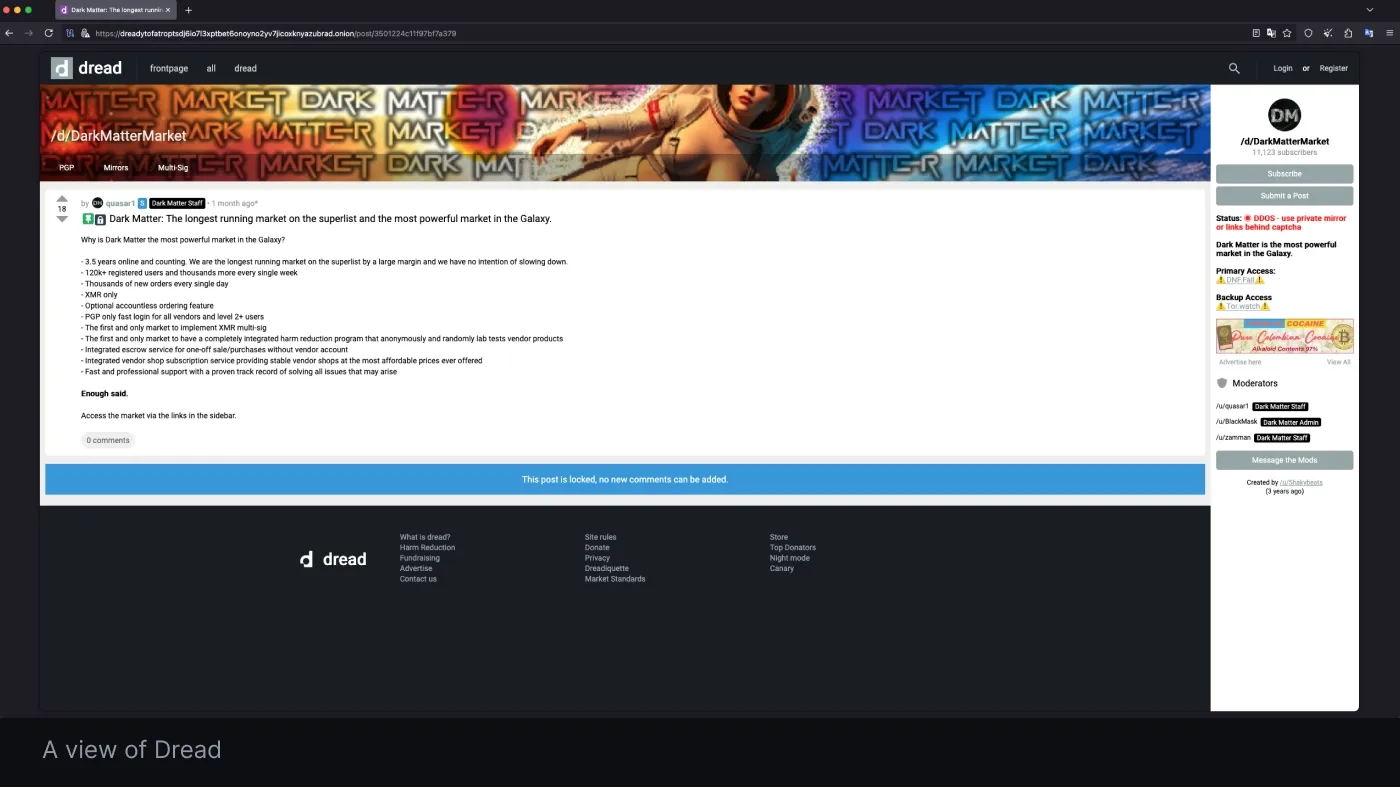
Subdreads. The core of the platform consists of over 2,000 specialized discussion sub-forums.
Decentralized moderation. Individual moderators manage subdreads, setting their own rules and guidelines.
User hierarchy. The structure flows from general members (content creators) to subforum moderators and finally to global administrators (like HugBunter).
Dread’s key features
Unlike other dark web forums, which often require paid invites or reputation checks, Dread is generally open to the public, but registration is required to post there. To maintain its status as a top-tier dark web resource, Dread employs advanced security features:
Distributed denial of service (
DDoS) protection. It employs the “EndGame” security system, a custom, open-source front end that uses advanced CAPTCHA and request filtering to resist heavy attacks.
Anonymity. The platform relies heavily on cryptographic identities to protect the privacy of its users.
Community moderation. Decentralized moderation allows the community to flag scams and unreliable vendors in real time.
Advanced security: PGP and encryption on Dread
Dread uses Pretty Good Privacy (PGP) as a cornerstone of its security architecture to mitigate risks like phishing and server-side compromise.
PGP-based authentication. Users can replace or augment traditional passwords with PGP signatures. During login, the server issues an encrypted challenge that only the user’s private key can decrypt. This means that even if a password is stolen, the account can’t be accessed without the physical private key (often stored in secure environments like Tails OS).
End-to-end encrypted messaging. Dread facilitates PGP-encrypted private messages (PMs). Communications, such as shipping details or sensitive exploits, are unreadable to admins, hackers, or law enforcement, even if the forum’s servers are seized.
Anti-phishing strategy. By prioritizing PGP identities over standard credentials, Dread protects valuable targets (such as vendors and researchers) from credential harvesting and man-in-the-middle (MitM) attacks.
What are the key topics on Dread?
The interaction between users on Dread creates a unique information ecosystem focused on:
Darknet market (DNM) data. This is the primary use of Dread. Users review
dark web marketplaces, track exit scams, and rank vendor reliability to mitigate financial risk.
Cybercrime. It is a central meeting point for hackers to coordinate ransomware-as-a-service (RaaS) attacks, trade zero-day exploits, and sell stolen databases or compromised credentials.
Financial fraud. There are extensive discussions on “carding" (credit card theft), money laundering techniques, and other types of payment-related fraud.
Illicit trade. There are also communities dedicated to the illicit trade of illegal substances, including their trafficking, manufacturing, and distribution.
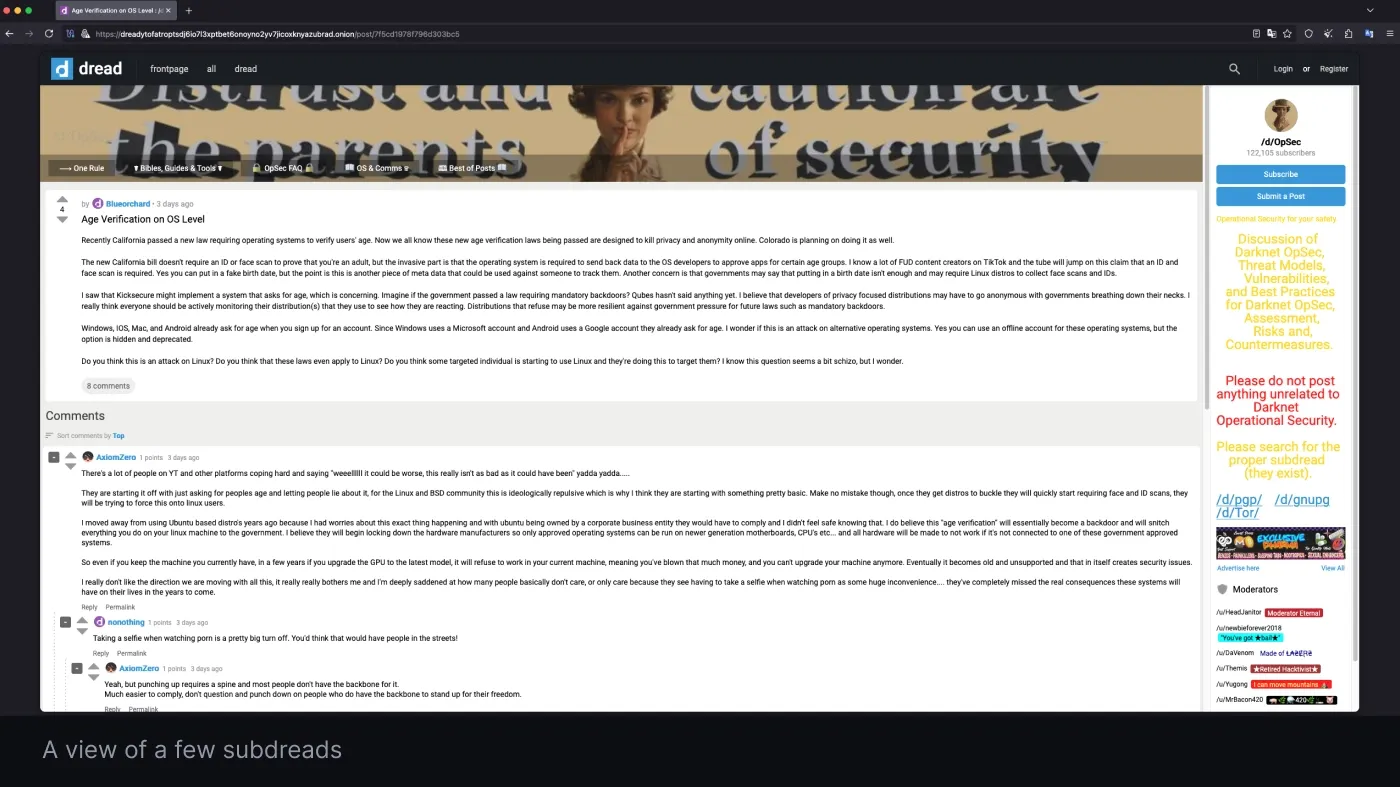
Operational security. This involves technical exchanges on maintaining anonymity, using privacy-focused cryptocurrencies like Monero, and safely navigating the Tor network.
General and advocacy discussions. The forum also hosts “innocent” discussions on human rights, video games, and internet privacy.
Related articles

Aistė MedinėOct 16, 20258 min read

Joanna KrysińskaDec 11, 20256 min read
Is accessing Dread illegal? Legal and ethical boundaries.
Although browsing Dread or using the Tor network is not illegal in many jurisdictions, including the US and most of the EU, the context and intent of your activity are what matter.
Passive observation vs. active participation. Simply viewing discussions on dark web markets or reading about new vulnerabilities for defensive purposes is generally considered legal research. However, engaging with illicit content, such as purchasing drugs, downloading malware, or soliciting cybercrime services, crosses the line into criminal activity.
The risk of an accidental click. Many threads on Dread contain links to illegal marketplaces or disturbing sites. Stumbling onto illicit content is not only a bad experience, but also a massive legal risk you’d rather avoid. Once a connection is made, proving to the authorities that you lacked criminal intent can be an incredibly difficult task.
Compliance. Even if legal, accessing .onion sites often violates corporate security policies. Your team should never access dark web forums from standard company devices or networks without explicit authorization and a dedicated, isolated environment.
Is it safe to browse Dread?
The Dread dark web forum is a hostile environment and rife with security risks designed to de-anonymize or compromise visitors.
Phishing and mirror attacks. Be extremely cautious of where you get your Dread onion links. Attackers frequently create fake “mirror” sites that look identical to the real forum, but are built to steal your login credentials or phish your PGP keys.
Malware distribution. Threat actors often share files, scripts, or leaked databases that have actually been weaponized with malware. Downloading anything from Dread onto a non-isolated machine can lead to immediate compromise.
De-anonymization. Poor operational security (OpSec)—such as enabling JavaScript, resizing your Tor browser window, or using a standard VPN instead of Tor—can leak your real IP address to the site administrators or law enforcement monitoring the node.
If you decide to conduct research on Dread, do it in a secure environment, using strong anonymity tools and protocols.
Why security teams use Dread for threat intelligence
The Dread forum is a critical source of dark web threat intelligence. By monitoring the platform, security analysts can identify attacks while they are still in the planning stage, rather than waiting to react after the fact.
Early warning of zero-day exploits. Hackers often discuss new vulnerabilities on Dread days or weeks before a patch is available. Monitoring these discussions gives security teams a head start on remediation.
Ransomware operator announcements. Major ransomware gangs use Dread to recruit affiliates, announce new victims, or leak samples of stolen data to prove their legitimacy.
Fraud and scam trends. Discussions about new methods for bypassing two-factor authentication (2FA) or exploiting specific banking apps help financial institutions adjust their fraud detection models.
Breach indicators. If users on Dread are asking for fresh logs or
combo lists related to your specific industry or company, it is a signal that you are being targeted.
Switch to automated dark web monitoring with NordStellar
Manually browsing the Dread forum is inefficient and dangerous. It exposes your organization to malware, legal liability, and the risk of inadvertent data leaks. If you decide to visit Dread, ensure you are following strict security protocols.
However, you shouldn’t have to risk your safety for threat intelligence. NordStellar’s Dark Web Monitoring solution continuously scans hacker forums, Telegram channels, and ransomware blogs to deliver critical, real-time insights about hidden threats.
Stop manually searching for threats. Let NordStellar do it for you. Gain full visibility into your external risks today. Try NordStellar for free.
Disclaimer: This article is published solely for educational and cybersecurity research purposes. It does not constitute legal advice nor endorse, encourage, or facilitate access to any illegal platform, service, or activity. Descriptions of illegal activities, including ransomware operations, financial fraud, illicit trade, and dark web markets, are provided to inform security professionals of the existing threat landscape. These descriptions should not be construed as instructions, solicitations, or facilitation of any unlawful act. The legality of accessing Tor network resources and dark web forums varies significantly by jurisdiction. Readers bear sole responsibility for ensuring their activities comply with all applicable laws before conducting any dark web research. Screenshots and references to third-party platforms are used for illustrative and journalistic purposes only and do not imply affiliation with or endorsement of any depicted content. To the fullest extent permitted by applicable law, NordStellar, its affiliates, employees, and contributors disclaim all liability for any legal consequences, security incidents, data breaches, or damages arising from reliance on the information contained herein or from any decision to access the described platforms. This article does not guarantee the accuracy, completeness, or currency of the information provided.

Joanna Krysińska
Senior Copywriter
Joanna's family has a history in math and engineering, and she loves explaining complicated technical ideas. She helps people understand how hackers think and how to stay ahead of them by concentrating on the human side of cybersecurity.