Summary: ASM 2.0 goes beyond simple asset lists to actively validate risks, pinpointing exactly where your external perimeter is exposed. See how it works.
Let’s be honest for a moment: seeing a vulnerability report can be stressful. But seeing thousands of vulnerabilities? That’s not just stressful—it’s useless.
In cybersecurity, vulnerability visibility without validity is just noise. For security teams, simply knowing what assets exist is no longer sufficient. The only question that matters is: which of these can be exploited right now?
NordStellar’s Attack Surface Management (ASM) 2.0 answers this directly. By trading passive inventory lists of legacy solutions for active risk validation, it distinguishes between the theoretically dangerous and the truly vulnerable. This allows you to stop patching blindly and start eliminating real risks.
Here is how ASM 2.0 works and what it means for your organization.
The problem: blind spots and “the alert fatigue”
Most security teams are trapped between two extremes: either a lack of visibility into shadow IT or an overwhelming number of alerts generated by scanners. For security leaders, this means one thing: they can’t see real threats. And you can’t protect what you can’t see.
On one side, the digital perimeter is expanding faster than it can be mapped. Forgotten subdomains and unauthorized cloud tools create blind spots that static scanners invariably miss. On the other hand, traditional scanners generate such a high volume of alerts that IT teams struggle to distinguish real threats from false ones. The result is "alert fatigue." Your team gets so many of these alerts that, when a real threat appears, it gets lost in the shuffle.
The old mechanisms of managing the attack surface are failing for several reasons:
Unidentified asset. Shadow IT and forgotten subdomains create blind spots that static scanners miss.
Inefficient manual processes. Verifying whether an alert is real requires hours of human time (manual checking), which is both expensive and inefficient.
Prioritization paralysis. When faced with thousands of alerts, lean teams struggle to identify which vulnerabilities can be exploited and which are merely distractions.
Outdated intelligence. Your organization’s attack surface changes constantly. Periodic reports become outdated the moment a new code deployment happens.
Let’s now explore how ASM 2.0 works in practice.
Related articles

Aurelija EinorytėJan 15, 20258 min read

Rūta TamošaitytėDec 16, 20256 min read
How NordStellar’s ASM 2.0 works
ASM 2.0 combines continuous asset discovery with active vulnerability validation.
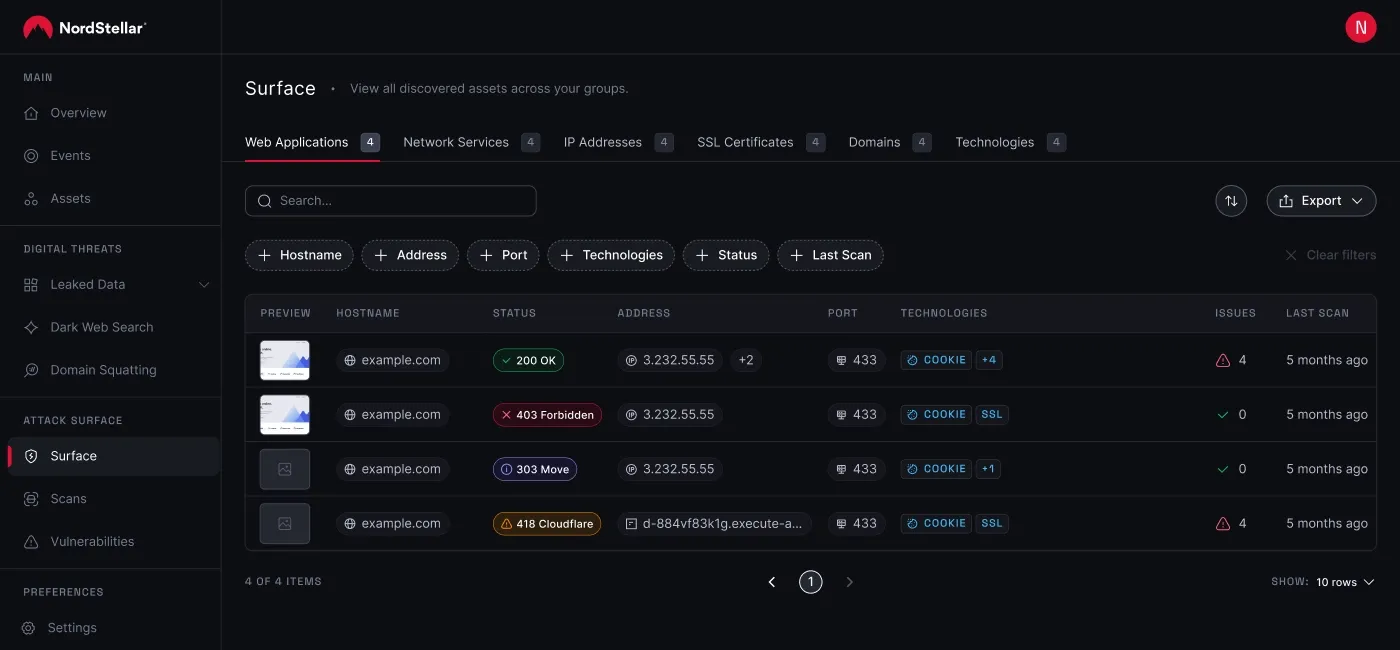
First, we map your infrastructure. We identify all assets exposed to the internet—from web apps and network services, to DNS configurations.
Then, we switch to an attacker’s perspective. Unlike passive techniques that only read version numbers, we use techniques such as active web fuzzing and dynamic application security testing (DAST). We safely simulate the behavior of a hacker.
Next, we verify whether a detected vulnerability—such as SQL injection or cross-site scripting (XSS)—can actually be exploited. Finally, we transform a list of possible threats into a concise, prioritized “hit-list” of risks.
Putting ASM into practice
Manual verification doesn’t scale. You cannot hire enough people to check every alert. ASM 2.0 automates the grunt work. Here is what it looks like for your security teams:
For security analysts. Stop chasing false positives. Instead, start your day by opening a dashboard of verified risks. Better yet, our AI-driven remediation guidance provides precise instructions for resolving issues. No more spending 3 hours on Google trying to figure out a patch for a legacy library.
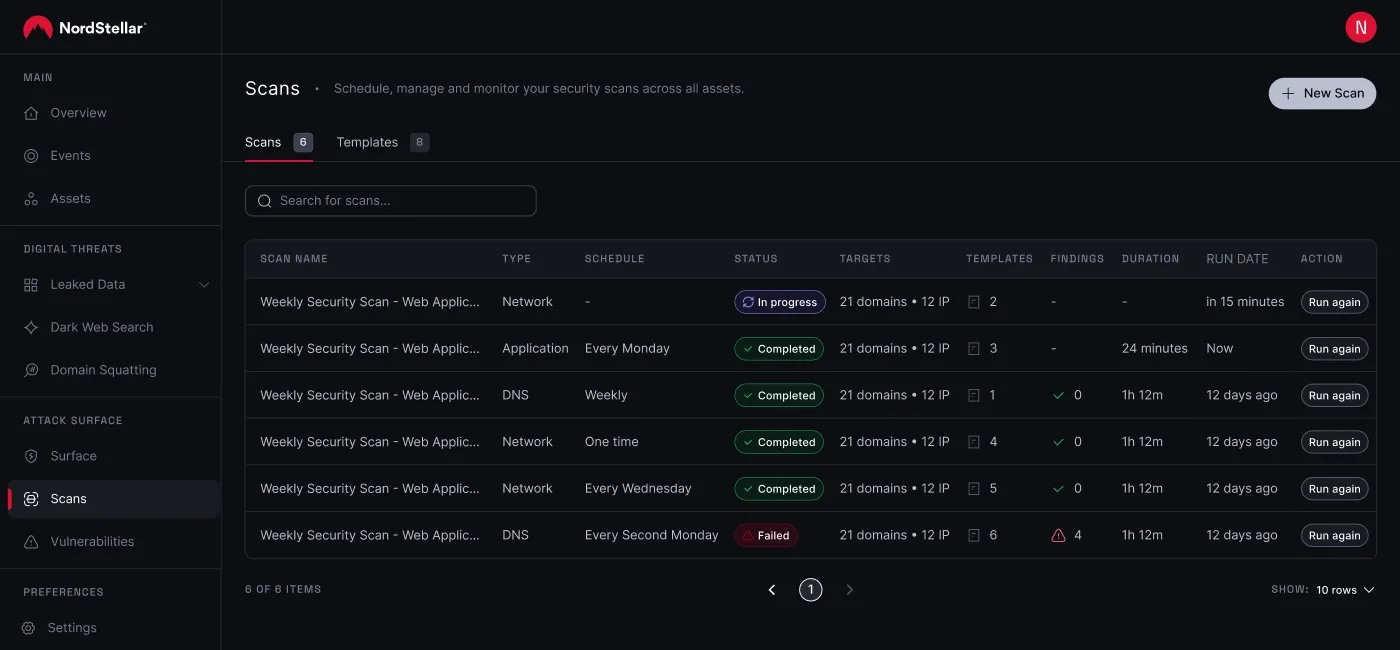
For security engineers. DevOps moves quickly, and security often slows it down. Not anymore. Trigger on-demand scans immediately after a deployment. Did a misconfiguration slip into production? You’ll catch it the moment it hits the internet, fixing it before an attacker even notices the door is open.
For the security managers. Walk into stakeholder meetings with a clear ROI. Instead of reporting, "We found 10,000 assets," you can report, "We closed 50 verified attack vectors." It proves you aren't just watching the network, but also hardening it.
Why ASM 2.0?
As the pressure to manage unknown assets and evolving vulnerabilities mounts, NordStellar puts you back in control. ASM 2.0 automatically translates dense scanning data into prioritized, actionable findings, so you know exactly which threats to address first.
No more false positives with active validation. By actively testing specific protocols, ASM 2.0 validates exploitability and significantly eliminates false positives, ensuring your team focuses only on verified threats.
Total coverage. From web applications to detailed DNS configurations, we eliminate the blind spots other solutions miss.
Flexible, on-demand scanning. Security is no longer bound by static schedules. Set automated schedules for baseline protection, or trigger instant scans immediately after deployments to verify your infrastructure the very moment it changes.
Automation-driven efficiency. NordStellar minimizes the need for manual, routine risk assessments, allowing your team to tackle strategic threats.
Prioritized risk list. Vulnerabilities are ranked by risk level, delivering a sorted "hit-list" of critical issues that demand immediate attention.
AI-powered remediation guidance. We don't just list problems; we help solve them. Get clear, AI-driven, step-by-step instructions to immediately fix vulnerabilities, bypassing hours of research.
Support for compliance requirements. ASM helps demonstrate your continuous commitment to industry regulations that require regular vulnerability assessments.
Stop drowning in the alert noise. Start fixing threats that are real. Try NordStellar for free to uncover shadow IT and address actual vulnerabilities before attackers find them.

Joanna Krysińska
Senior Copywriter
Joanna's family has a history in math and engineering, and she loves explaining complicated technical ideas. She helps people understand how hackers think and how to stay ahead of them by concentrating on the human side of cybersecurity.