Summary: Many risks remain invisible, but with proactive threat detection solutions, you can detect them and stop a cyberattack in its early stages.
Cybercriminals usually strike when and where an organization least expects it. It is obvious. But still, for many businesses, the first sign of trouble is a formal security alert triggered only after an attack is already in progress.
This reactive approach is no longer enough. To stay secure, organizations must move from defensive security to proactive threat detection. Identifying vulnerabilities and leaked data before they can be used against you gives your business a tactical advantage.
Let’s explore what proactive threat detection is, how it works, and how your business can implement it.
What is proactive threat detection?
Proactive threat detection is a holistic strategy that focuses on the data-driven search for security gaps and vulnerabilities before hackers find them. Unlike a reactive defense, this approach allows for intervention during the earliest stages of an attack, often before a data breach occurs.
Threat hunting, attack surface management, and vulnerability assessment are the 3 key parts of the proactive threat detection strategy.
Proactive threat detection vs. reactive defense
The difference between these strategies lies in the trigger.
Reactive defense is a response to a security alarm. It is triggered only after an incident has already begun.
Proactive threat detection is tactical. Based on the insights from deep and dark web sources, it detects threats that have bypassed perimeter defenses but have not yet triggered a formal alert.
How proactive threat detection works
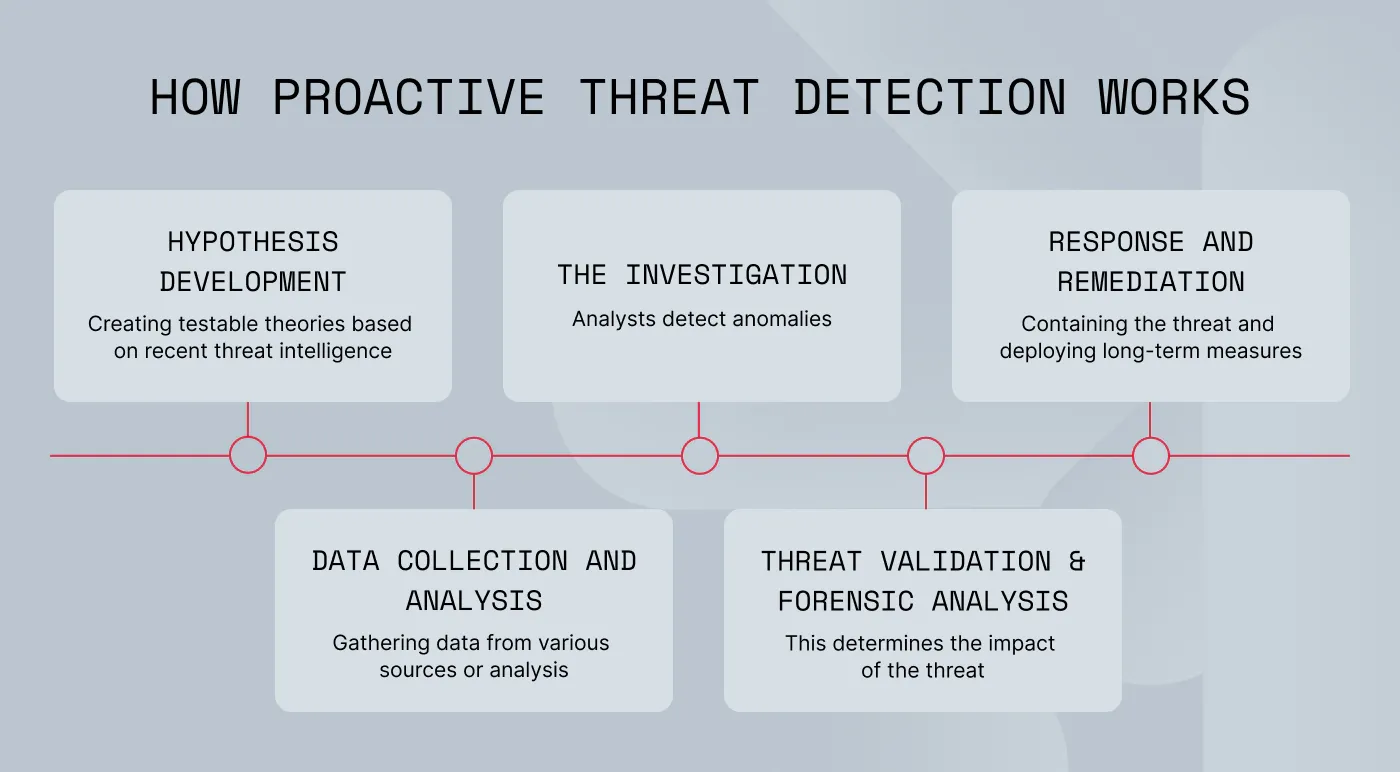
In short, proactive threat detection is a hypothesis-driven investigation. Here is how this 5-stage process looks:
Hypothesis development. Security teams begin by creating testable theories on how hackers could target an organization. These theories are based on recent threat intelligence data and known organizational risks.
Data collection and analysis. Teams then assemble a comprehensive view of the threats. To do so, they gather security telemetry from various sources, such as dark web monitoring solutions, endpoints, and cloud platforms.
The investigation. Analysts use advanced tools to examine the collected data to verify or disprove their initial theories. The idea is to separate a genuine threat from the noise of routine network activity.
Threat validation. Once a risk is confirmed, it is validated through forensic analysis. This determines the reach and impact of the intrusion and the techniques used by the attacker.
Response and remediation. Finally, the team moves to contain the threat. This involves, for example, invalidating stolen session cookies or resetting compromised credentials. Long-term measures are then deployed to prevent the same attack from happening again.
Why does proactive threat hunting matter for businesses?
The global average cost of a data breach reached $4.44 million in 2025. In the face of these escalating financial risks, organizations should move to preventive measures. Proactive threat detection can lower the recovery, legal, and operational costs. Here are its key benefits:
Faster threat detection. Better visibility into hidden threats and potential vulnerabilities helps neutralize risks faster.
Reduction of false alerts. Getting real-time alerts enables teams to focus on the actual threats and intervene immediately.
Protection of business reputation. Spotting brand impersonation (
cybersquatting) or leaked VIP information early helps maintain customer trust and prevents long-term damage to the brand.
Simplified compliance. With continuous threat monitoring, you can demonstrate due diligence to regulators and comply more easily with laws such as GDPR, DORA, NIS2, SOC 2, and ISO 27001.
Core elements of a proactive threat detection strategy
By integrating multiple security layers into your proactive threat detection strategy, your team gains real-time visibility to identify and neutralize threats before they escalate.
Asset monitoring and vulnerability assessment
Effective threat detection starts with managing all internet-facing assets, such as websites, servers, and cloud resources. Running a regular vulnerability assessment—a comprehensive security check of your network and applications—helps you discover system flaws that hackers are looking for. This scanning process detects security gaps and allows you to address them.
Related articles

Rūta TamošaitytėAug 28, 20258 min read

Agnė SrėbaliūtėFeb 25, 20268 min read
Setting up real-time alerts
Getting a notification the moment sensitive data is exposed can save your organization from a damaging breach. This immediate awareness is only possible when you have a clear view of your entire network. Proactive threat detection tools provide real-time visibility into potential vulnerabilities.
For example, NordStellar’s threat intelligence platform continuously monitors over 40,000 deep and dark web sources, including hacker forums, ransomware blogs, and Telegram channels. Cross-referencing your company’s assets against these sources in real time gives you the insights necessary to take action before attackers do.
Attack surface management
Managing all access points to your network and systems is critical for a proactive threat detection and response strategy. To support this, solutions like Attack Surface Management (ASM) automatically discover internet-facing assets via DNS enumeration, web crawling, and open-source intelligence (OSINT) techniques. Unlike traditional endpoint detection tools, ASM also covers hidden areas like web subdomains and shadow IT, which makes it a fit for complex cloud and hybrid networks.
Behavior analysis and anomaly detection
User and entity behavior analytics (UEBA) allows you to establish a baseline of normal user activity, such as login times and access patterns. This makes it easier to spot weird patterns that signal a malicious attempt to gain unauthorized access, such as:
Unusual login activity from unrecognized devices, strange locations, or odd hours.
Data exfiltration signals, such as unusual volumes of data transfers, may indicate a breach.
Regular security audits and penetration testing
Conducting regular security audits and penetration testing provides a reality check for your defenses. While audits ensure compliance with standards like ISO 27001, penetration tests actively simulate an attack to see how your systems hold up under pressure. These tests help you understand the actual risk of an incident and allow you to strengthen your security posture based on real-world findings.
Employee training and awareness programs
Proactive threat detection requires more than technology. IBM reports that 95% of data breaches are caused by human error. Therefore, building a resilient human firewall is essential to protecting your organization. If you teach your staff how to recognize phishing and social engineering tactics, you can avoid accidental infections. Also, by simulating real-world attacks, you can measure employee security awareness and ensure your entire team acts as a proactive defense layer for your organization.
Proactive threat detection: best practices for long-term security
To maintain a proactive defense, consider the following best practices to ensure your business is one step ahead of threats:
Secure access to threat intelligence. A proactive strategy is only as effective as the data behind it. Give your team a constant feed from the deep and dark web to identify indicators of compromise before they are used in an attack.
Monitor emerging attack vectors. Recently, there was an
84% increase in reported emails delivering infostealer malware, which shows that cybercriminals are very creative. Stay updated on new malware and phishing methods to prevent being caught off guard.
Maintain clear documentation and response playbooks. Speed is everything when a threat is detected. With documented incident response plans and automated workflows, your team can move from detection to remediation at once.
Foster a security-aware culture. Regular, engaging training reduces the risk of human error and turns your staff into an active part of your defense.
Choosing the right partner for proactive threat detection
When evaluating threat intelligence management platforms, prioritize these core capabilities:
Visibility into hidden threats. Ensure the solution monitors a wide range of sources, including dark web forums, Telegram channels, and infostealer logs.
Real-time alerts. Getting a notification about a threat can actually stop an attack, even if it has already started. Look for platforms that offer real-time monitoring and instant alerts.
Scalability and deployment. A flexible, cloud-based security solution is often preferred as it adapts to the needs of growing businesses without the added complexity of on-premises hardware.
Integration and efficiency. Choose a platform that centralizes breach, dark web, and attack surface intelligence. Seamless integration with existing SIEM/SOAR solutions is essential for streamlined workflows.
Vulnerability prioritization. The platform should help you identify the biggest dangers through automated asset discovery and
vulnerability management, not just list risks.
Stop guessing and start seeing your business through an attacker’s eyes. Try NordStellar for free to discover hidden dark web threats and vulnerabilities targeting your organization right now.

Joanna Krysińska
Senior Copywriter
Joanna's family has a history in math and engineering, and she loves explaining complicated technical ideas. She helps people understand how hackers think and how to stay ahead of them by concentrating on the human side of cybersecurity.