Summary: ASM helps teams discover internet-facing assets, monitor changes, and prioritize fixes to reduce exposure across cloud, apps, and vendors.
A new product team launches a microsite for a campaign. They spin up a subdomain, connect a third-party form, and ship fast. Two months later, that forgotten subdomain still points to an old cloud bucket, and the API key in the page source still works. No one meant to create risk—it just happened.
The complexity of modern digital environments makes it challenging for organizations to secure their attack surface. Security teams keep asking the same question: What’s exposed right now—and what has changed since yesterday?
IBM’s Cost of a Data Breach Report 2025 puts the global average breach cost at $4.44M, driven largely by “lost business” and post-breach response costs. In that same report, breaches involving stolen or compromised credentials took the longest to identify and contain—241 days on average.
Cybercriminals don’t care whether an asset is “owned” by IT, marketing, DevOps, or a vendor. If it’s reachable, it’s part of your risk picture.
Key takeaways
Attack surface management (ASM) is a continuous process of discovering and tracking the assets you expose, then finding and fixing the security gaps attackers can use.
Your attack surface includes anything attackers can reach or abuse: domains, apps, cloud services, identities, misconfigurations, and vendor connections.
Visibility matters because unknown or unmanaged assets create blind spots, and blind spots create incidents.
Common risks include exposed admin panels, forgotten subdomains, open ports, leaked credentials, and shadow IT.
Risk assessment is key to classifying, analyzing, and assigning risk scores to vulnerabilities within your asset inventory. This helps prioritize remediation as part of a broader cybersecurity strategy.
Attack Surface Management is about continuous monitoring, not a one-time inventory, because your attack surface can change within a week or an hour.
What is attack surface management?
Attack surface management (ASM) is the practice of continuously finding what your organization exposes to the internet—and then reducing that exposure. It helps security teams spot assets that shouldn’t be public, aren’t owned by anyone, or haven’t been maintained. In simple terms, if you know what’s out there, you can fix what increases risk.
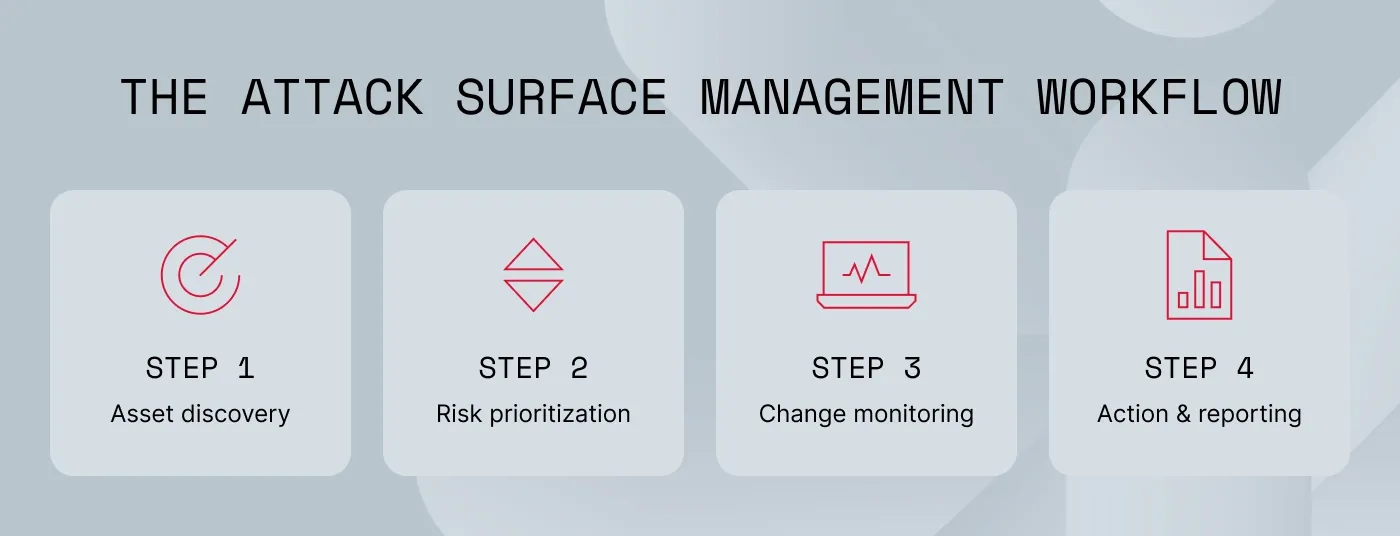
ASM usually runs as a continuous cycle: discover external assets, assess risk, prioritize what matters, remediate, and keep monitoring.
ASM focuses on internet-facing assets because they can be reached without internal access, they change fast (cloud services, vendors, new launches), and they can stick around long after the team that created them is gone.
Known vs. unknown assets where exposure slips through
Most organizations have a solid handle on known assets—registered domains, approved SaaS tools, production apps, and documented infrastructure.
The bigger risk often sits outside that list. Unknown assets show up through shadow IT, abandoned development stacks, vendor portals, test environments, and forgotten subdomains. They may still be reachable, but they don’t get the basics like patching, logging, or clear ownership. And when you can’t see them, you can’t secure them.
The gap ASM that is built to close is about the difference between what’s documented and what’s exposed.
Types of attack surfaces
Security teams often group attack surfaces into three broad categories: digital, physical, and human. ASM focuses on the digital attack surface, but incidents often combine all three:
Digital exposure of domains, cloud assets, applications, identities, and credentials.
Physical exposure that includes devices, offices, and hardware access points.
Human exposure, such as phishing, social engineering, and credential theft.
While attack surface types describe risk categories, IT teams usually organize their work by exposure scope—external, internal, and third-party assets.
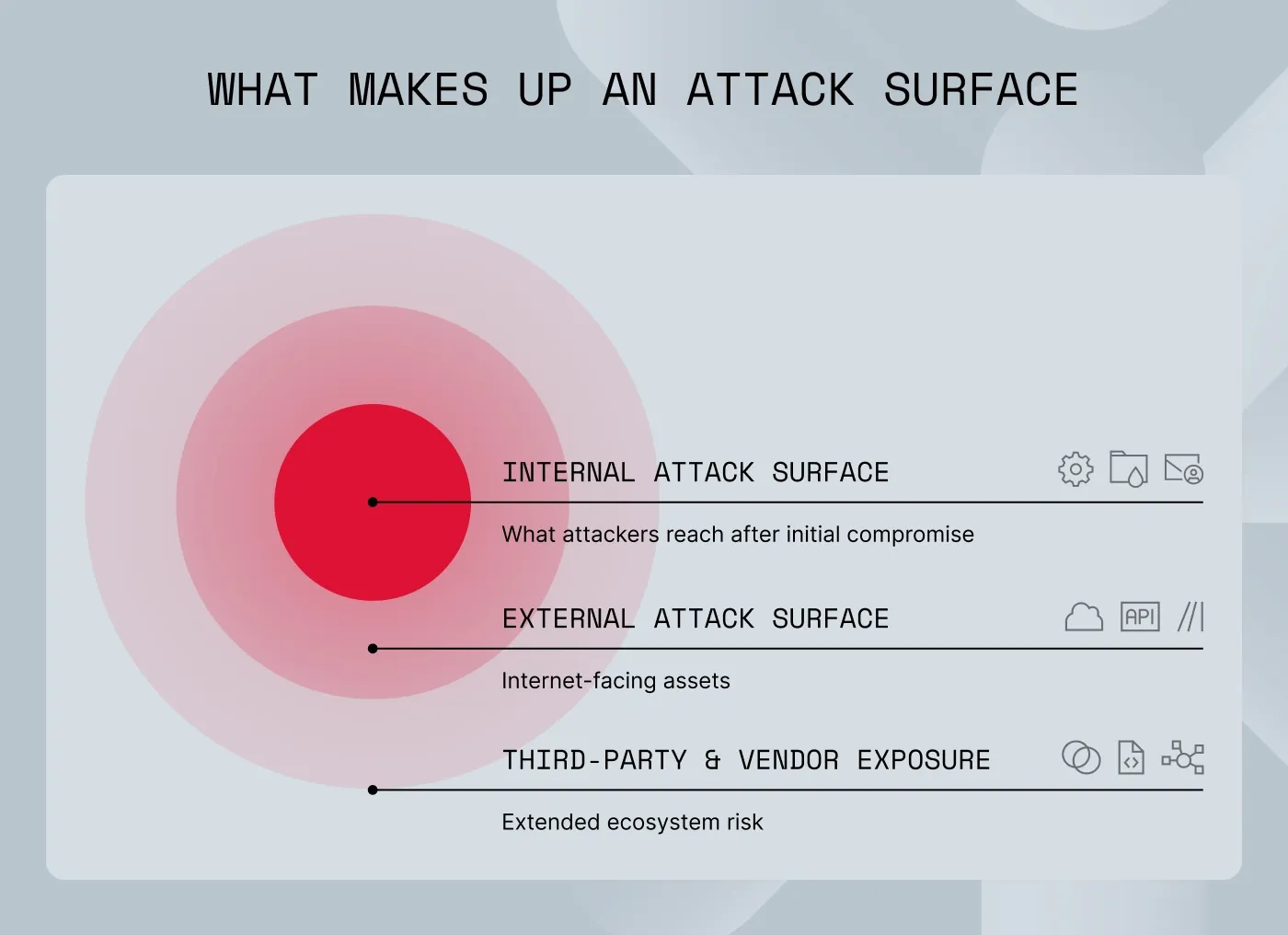
What makes up an attack surface
An attack surface is every point an unauthorized user could exploit to enter a system, extract data, or cause harm. It spans internet-facing assets, internal systems, and third-party services. Data sprawl and rapid asset growth make it larger—and harder to manage.
External attack surface
External attack surface management typically covers public-facing assets such as:
Domains and subdomains (including forgotten ones)
Cloud services and storage
Web applications and APIs
IP addresses and exposed services
A common failure occurs when a subdomain is created for short-term use, DNS is pointed to a temporary service, and ownership is never reassigned. The infrastructure persists, but patching, credential rotation, and access control fall behind.
Organizations must continuously assess their attack surfaces to identify and patch critical vulnerabilities before threat actors can exploit them.
Internal attack surface
Internal attack surface management focuses on what becomes reachable after initial access—whether through phishing, credential theft, or insider misuse. This includes:
Internal systems
Administrative tools
Identity stores
Access permissions
Configuration states
Shadow IT inside the network
In many environments, identity and permission sprawl create more exploitable paths than missing patches. Stale accounts, reused credentials, and excessive privileges regularly turn minor footholds into major incidents.
Third-party and vendor exposure
Vendors expand your attack surface even when your internal controls are strong. Third parties and supply chain complexity are major risks because exposure grows through:
Shared platforms
API integrations
Outsourced services
Analytics tags
Embedded scripts
Partners with data or network access
Related articles

Rūta TamošaitytėDec 16, 20256 min read

Aurelija EinorytėJan 15, 20258 min read
ASM is not just technical hygiene. It directly impacts operational resilience, financial risk, and the decisions leadership makes every day.
Lower breach risk and faster containment
When you continuously monitor exposed assets and credentials, hackers lose easy entry points. Security teams can detect exposures earlier, which shortens dwell time—the time a hacker spends in your system— and limits the blast radius. In the long run, that can directly lower incident costs and reduce recovery time.
Fewer surprise outages
Unmonitored exposure often leads to service disruption—whether it’s a ransomware staging point, a hijacked admin panel, or an abused API. Continuous attack surface management prevents downtime by surfacing these weak points before they are exploited.
Better audit readiness
Modern regulations and cybersecurity compliance requirements now expect you to prove you have visibility into external exposure. ASM provides evidence of continuous monitoring and remediation tracking. This makes it much easier to walk an auditor through your security narrative and validate your controls.
Stronger brand and partner trust
Public breach disclosures damage reputation and partner confidence. Proactive exposure reduction is far less costly than public incident response. ASM helps shift security posture from reactive to preventative.
How attack surface management works in practice
In mature environments, ASM isn't just a tool you turn on. It’s an operating loop that feeds daily security workflows.
1. Continuous asset discovery
Security teams use ASM platforms to map domains, subdomains, certificates, IP space, cloud assets, and exposed services—including assets not present in internal inventories. The goal is not just to list assets, but to figure out who owns them and why they are exposed.
2. Risk identification and prioritization
Findings are evaluated based on how easy it is to exploit them and their impact, not just a severity label. Open ports, outdated technologies, exposed admin interfaces, certificate anomalies, and risky third-party links are ranked so teams fix what reduces risk first.
3. Ongoing monitoring for changes
Attack surfaces tend to drift. New DNS records appear, storage permissions change, certificates rotate, and vendors deploy new portals. Monitoring flags these changes so teams don’t start security assessments from scratch every time.
4. Alerts and reporting that drive action
In effective solutions, ASM feeds ticketing systems, SecOps queues, and cloud security pipelines. If exposure data lives only in a dashboard, remediation slows down. If it enters workflow tools, risk decreases.
Who owns ASM inside a company?
ASM works best as a shared solution with clear accountability.
Security and IT teams usually own the ASM solution itself. They define scope, set monitoring rules, triage exposure findings, and track risk reduction over time. Their role is coordination and prioritization, not fixing every issue directly.
Engineering, cloud, and DevOps teams typically own remediation. They close ports, rotate secrets, remove unused services, fix configurations, and adjust pipelines so exposures are not reintroduced.
Risk and compliance teams translate ASM outputs into governance evidence. They map exposure controls to regulatory requirements, document risk acceptance decisions, and demonstrate continuous oversight during audits.
A practical rule seen in high-maturity organizations: security owns visibility, engineering owns fixes, compliance owns proof.
Tools used for attack surface management
Teams usually combine several attack surface management tools instead of relying on a single scanner.
ASM platforms. Centralize discovery, exposure monitoring, and prioritization across internet-facing assets.
Automated asset discovery. Expand coverage in complex environments where infrastructure changes quickly.
Cloud and domain monitoring. Track DNS changes, certificate shifts, new subdomains, risky storage settings, and exposed services.
Risk scoring and prioritization. Connect exposure to business impact so teams fix what matters, not just what’s loud.
ASM is most effective when paired with vulnerability management. ASM finds what exists and is exposed; vulnerability management analyzes what is weak on known systems.
How NordStellar fits into your ASM workflow
NordStellar brings ASM into a broader external exposure view: one platform that consolidates internet-facing exposure with leaked credentials and threat signals—so teams spot risk early and act within the context.
Where it helps in practice:
External visibility for fast-moving teams. When domains, cloud services, and apps change often, you need asset discovery and monitoring that keeps up.
Prioritize the fixes that reduce exposure fastest. Tie exposed services and outdated technologies to remediation work, then track progress over time.
Connect exposure to real attacker activity. If leaked credentials or breach signals appear alongside exposed assets, it’s easier to decide what needs immediate action and what requires a more detailed look.
If you want a starting point for actionable findings, external vulnerability scanning is a useful companion for teams that seek visibility into internet-facing weaknesses without heavy setup.

Agnė Srėbaliūtė
Senior Creative Copywriter
Agne is a writer with over 15 years of experience in PR, SEO, and creative writing. With a love for playing with words and meanings, she crafts content that’s clear and distinctive. Agne balances her passion for language and tech with hiking adventures in nature—a space that recharges her.