Summary: In a double extortion attack, hackers first steal your data, then encrypt it and threaten to leak it. Visibility into your attack surface can help prevent it.
Double extortion ransomware attacks your business in two ways. First, hackers steal and encrypt your data. Then, they threaten to leak it if a ransom isn’t paid.
This scenario has become the cybercrime standard for one simple reason: it is highly effective. Even organizations with perfectly updated backups often feel forced to pay just to avoid the legal and reputational consequences of a massive data leak.
The profitability of this model is clear. According to recent research from NordStellar, ransomware incidents surged in 2025, with 9,251 cases recorded on the dark web—a 45% increase from 2024.
In this article, we will examine how double extortion ransomware attacks work and the best strategies to protect your business from them.
Key takeaways
Double extortion is a ransomware attack where threat actors exfiltrate the victim’s sensitive data before encrypting it, and then threaten to leak it if a ransom isn’t paid.
While backups can restore systems, they can’t prevent stolen data from being sold or leaked on the dark web.
Almost every ransomware incident since 2019 has involved double extortion tactics.
Organizations can prevent double extortion attacks by using proactive security measures such as zero-trust architecture, robust data loss prevention (DLP), and attack surface management solutions.
You can stop a ransomware attack in its early stages by identifying vulnerabilities before they are exploited.
The evolution of ransomware attacks: from encryption to exfiltration
Historically, ransomware was a straightforward “exchange.” Hackers would lock your data or devices and demand a ransom for the decryption key. Back then, paying the ransom was usually enough to end the ordeal and regain access to systems.
As organizations got better at maintaining regular backups to avoid paying the ransom, cybercriminals changed their playbook. They switched to a “name and shame” strategy:
Double extortion ransomware attacks. First, threat actors exfiltrate (steal) sensitive data, then encrypt it and threaten to publish it on dark web leak sites (DLS) if the victim doesn’t pay.
Triple extortion ransomware attacks. In these attacks, cybercriminals use stolen data to harass your customers or business partners, weaponizing your entire supply chain.
While “traditional” encryption-based ransomware attacks are declining, almost every ransomware incident since 2019 has involved double extortion tactics. This shift means organizations should focus on preventing data theft just as much as preventing the initial infection.
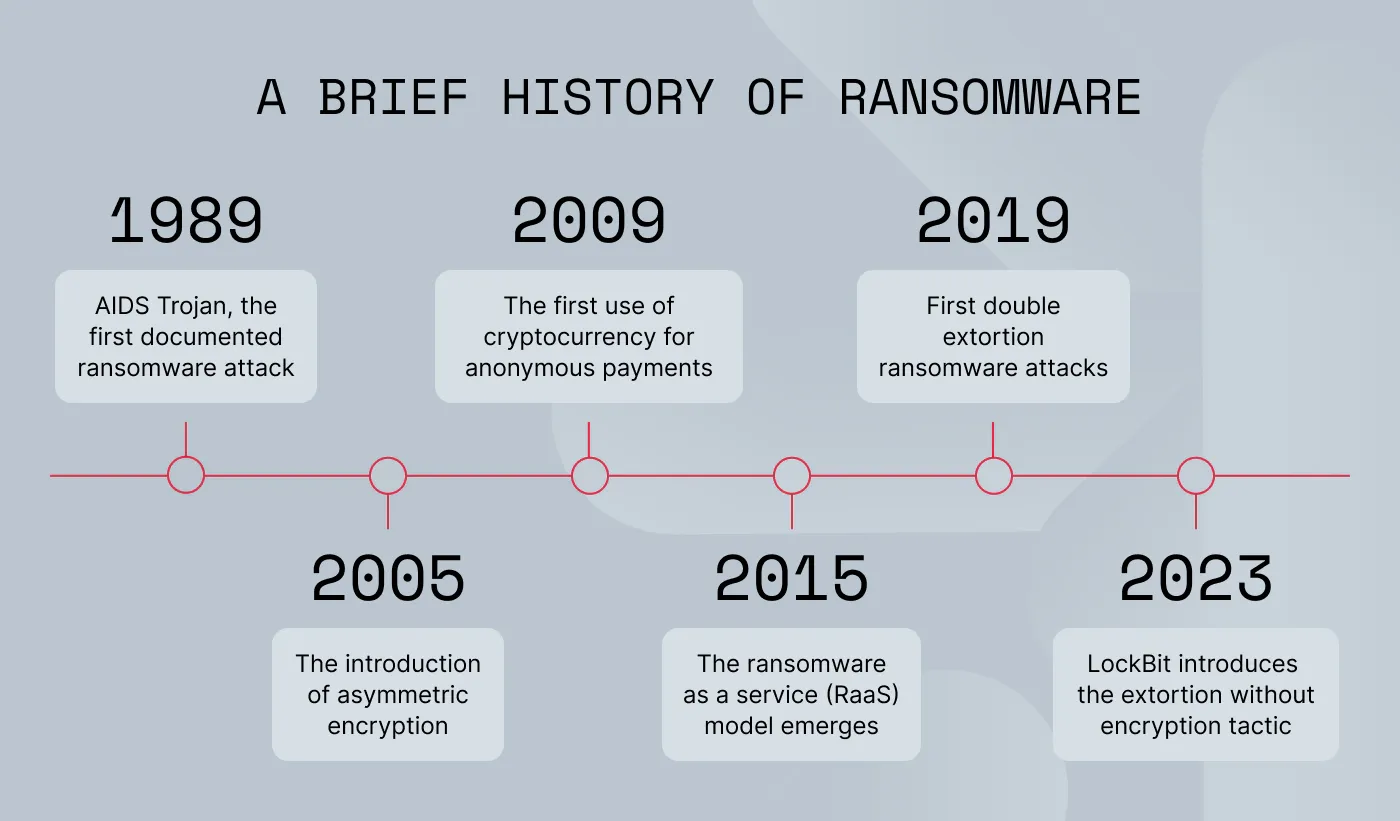
A brief history of ransomware
The transformation of ransomware shows how quickly attackers adapt to new security measures.
1989. The first documented ransomware attack, AIDS Trojan, was distributed via floppy disks. It was primitive. It only hid file directories on the victim’s device and demanded $189 to unhide them. However, the victim could easily reverse the damage without paying the ransom.
2005. Ransomware gangs from Russia and Eastern Europe introduced asymmetric encryption. This made it impossible for victims to recover data on their own. Ransomware began to spread around the world.
2009. The arrival of cryptocurrency gave cybercriminals a way to receive anonymous payments that bypass banks and government regulations.
2015.
The ransomware-as-a-service (RaaS) model emerges.
Ransomware groups like Qilin, Safepay, and
Akira “industrialized” the process, providing their affiliates with automated, ready-made tools for stealing data.
2019. Encryption became less effective as companies improved their backups. In response, attackers added data theft and public “leaks” to their tactics, creating double extortion ransomware.
2023. Some groups, like
LockBit, introduced the
tactic of extorting without encrypting. They use infostealer malware to hold data hostage without ever locking the victim’s system.
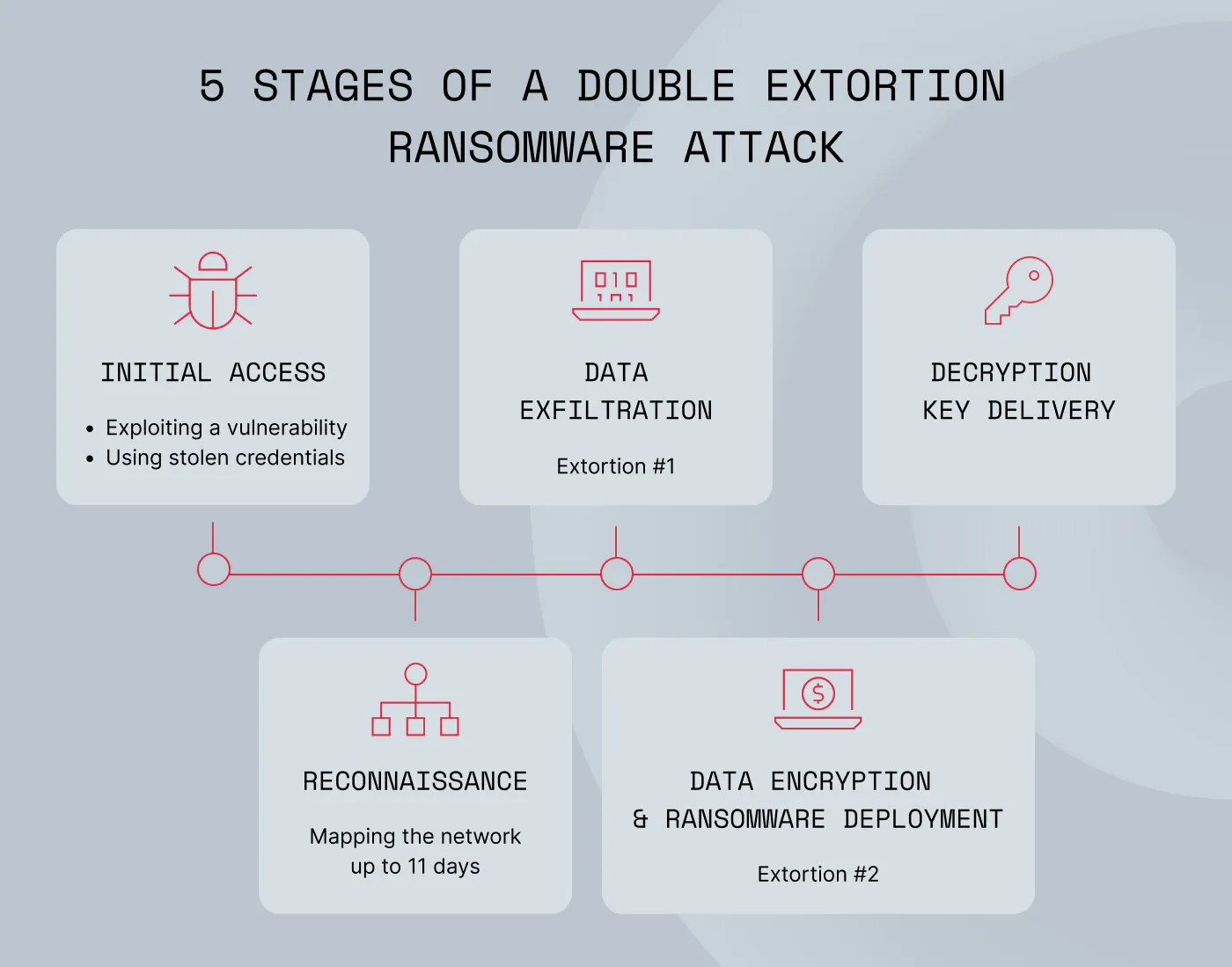
How double extortion ransomware attacks unfold
Double extortion is a multi-stage process in which cybercriminals threaten to leak stolen data to put immense pressure on victims.
Here is how this attack sequence typically plays out:
Stage 1: Initial access and reconnaissance
Attackers often gain a foothold in your network by using stolen credentials purchased from infostealer logs or by exploiting unpatched remote access points like virtual private networks (VPNs) and the Remote Desktop Protocol (RDP). They can also use techniques, such as SQL injection or remote file inclusion (RFI).
Once inside, hackers spend an average of 7–11 days silently mapping the network, searching for the most sensitive and valuable assets.
Stage 2: Data exfiltration (the first extortion)
Before encrypting any files, threat actors steal the victim’s data. They may use legitimate, pre-installed system tools in living off the land (LotL) attacks, like Rclone and Rsync, to transfer large volumes of sensitive information to their own servers.
Stage 3: Data encryption (the second extortion)
After securing the data, the attackers deploy ransomware. They use robust algorithms, such as AES-256, to encrypt the victim’s systems and files. This way, they paralyze the organization’s operations.
Stage 4: The ransom demand
Threat actors leave a note in the form of a text file or image on the victim’s system. This message includes proof of the stolen data, demands for payment in cryptocurrency, a deadline, and instructions on how to contact the attackers. The message also threatens to leak the stolen data on dark web forums.
Stage 5: Payment verification and decryption key delivery
Attackers provide a unique Bitcoin wallet address for payment. They then verify the transaction on the blockchain. If the victim pays, the hackers provide a decryption key. However, there is never a guarantee that they will actually delete the stolen data.
Related articles

Agnė SrėbaliūtėFeb 25, 20268 min read

Rūta TamošaitytėDec 16, 20256 min read
The impact of double extortion attack (and why it creates more risks than “traditional” ransomware)
Double extortion ransomware causes more than just operational downtime. It creates risks that can affect an organization for years. Because the threat involves both data encryption and data theft, its consequences affect every part of the business.
Financial and regulatory costs. The impact goes beyond the ransom itself. Organizations may face remediation expenses, lost revenue from downtime, and fines from regulations like GDPR, NIS 2, or CCPA.
Reputational damage. Data leaks impact customer trust more profoundly than temporary system outages. Once sensitive data is exposed on the dark web, the resulting damage to brand equity can lead to long-term customer churn.
Legal risk. Data theft often triggers mandatory breach notifications. This can result in class-action lawsuits if, for example, Personally Identifiable Information (PII) is compromised.
Loss of intellectual property. In sectors like technology or manufacturing, the theft of trade secrets or intellectual property can damage market positioning.
Uncertain recovery. Even if an organization has backups or chooses to pay, full data recovery is never a certainty. Data may become corrupted during encryption or simply be withheld by the attackers.
How to prevent double extortion ransomware attacks
To shrink your attack surface, you should implement a multi-layered security strategy. The Cybersecurity and Infrastructure Security Agency (CISA) recommends several key measures to prevent ransomware attacks:
Zero-trust architecture. Adopt the “never trust, always verify” approach to restrict access to your most sensitive data.
Egress filtering and data loss prevention (DLP). Monitor for unusual outbound data spikes, such as large volumes moving to unrecognized IP addresses during off-hours.
Data encryption. Encrypt sensitive information at rest and in transit.
Access controls. Apply the principle of least privilege to ensure that even if an account is compromised, the attacker’s access to data is restricted. Deploy phishing-resistant multi-factor authentication (MFA) to block attackers using stolen credentials.
Endpoint detection and response (EDR) solutions. Use EDR to identify ransomware during the reconnaissance phase, before data theft even begins.
Monitoring for indicators of compromise (IOCs). Actively track unusual network traffic or communication with command-and-control (C2) servers. Early detection of these signals can stop an attack during the initial stages.
Network segmentation. Divide your network into zones to limit an attacker’s ability to move laterally if they get inside.
Prevent ransomware attacks with NordStellar
Visibility is your first line of defense against double extortion ransomware. NordStellar’s threat exposure management platform provides a central view of your attack surface and helps you manage it with insights instead of speculation. This means you can verify the actual vulnerabilities and neutralize threats to prevent ransomware deployment.
Fix your attack surface before hackers find vulnerabilities
Move to continuous, automated oversight with Attack Surface Management (ASM). With ASM, you go from reactive to proactive security, which means you can intervene even at the earliest stages of a ransomware attack. This is what you get:
Visibility of every external asset. Continuous discovery minimizes exposed security gaps in external assets that ransomware attackers could exploit for initial access.
Automated threat detection. Get threat intelligence on misconfigurations, unpatched CVEs, exposed admin panels, or compromised credentials, so you can fix them before they are exploited.
Prioritized risk lists. Vulnerabilities are ranked by actual risk, which gives teams a sorted “hit-list” of critical flaws that could lead to ransomware deployment.
Insights into exploitable vulnerabilities. You can stop chasing false positives and focus on real threats.
Prevent double extortion ransomware before it starts. Reveal what hackers already know about your business and neutralize threats now. Try NordStellar for free and take control of your organization's attack surface today.

Joanna Krysińska
Senior Copywriter
Joanna's family has a history in math and engineering, and she loves explaining complicated technical ideas. She helps people understand how hackers think and how to stay ahead of them by concentrating on the human side of cybersecurity.