Summary: Strategic threat intelligence helps leaders understand cyber risks, prioritize security investments, and anticipate the next big threats through high-level analysis of attackers, trends, and business impact.
Cyber threats rarely affect only the security team. A ransomware group targeting a supplier can disrupt operations. A leak in an infostealer log can expose employee credentials. A new regulation can turn a security gap into a board-level risk. Therefore, strategic threat intelligence gives a clear view of which external threats deserve attention, where the business is exposed, and what decisions should come next.
Many teams still associate threat intelligence with feeds, indicators, and technical investigations. Those inputs matter, but they do not answer the executive questions, such as: Which threat trends are most relevant to the business this year? Which regions, vendors, or business units are most exposed? Where should the company invest first to reduce risk?
Strategic threat intelligence answers those questions. It helps CISOs, boards, risk committees, and senior leaders make better decisions. Instead of focusing only on what to block today, it shows which risks matter most over time and helps shape security planning, resilience efforts, and business strategy.
Key takeaways
Strategic threat intelligence helps leaders understand which cyber risks are most significant to the business.
Rather than day-to-day detection, threat intelligence focuses on long-term trends, industry patterns, threat actors, and regulatory impact.
Threat intelligence supports boards, CISOs, risk committees, and senior leadership in making security decisions.
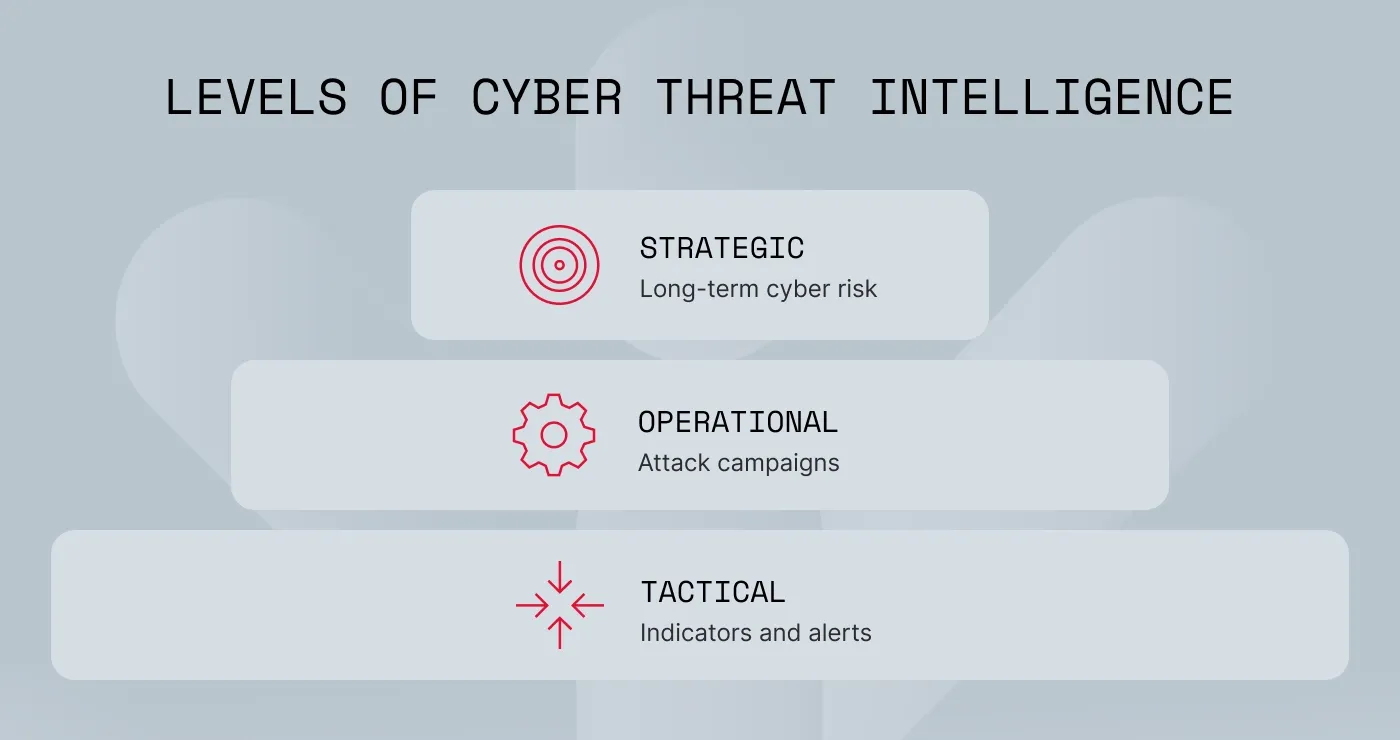
Strategic threat intelligence differs from tactical threat intelligence and operational threat intelligence in scope, audience, time frame, and output.
A strong program starts with business-aligned intelligence requirements and ends with concise reporting that supports leadership decisions.
What is strategic threat intelligence?
Strategic threat intelligence is a high-level analysis that helps business leaders understand cyber risks, assess their impact, and make informed security decisions. In simple terms, this definition focuses on turning threat data into insights that guide business and security strategy.
In practice, strategic cyber threat intelligence looks beyond isolated alerts or technical artifacts. It examines broader patterns such as threat actor activity, industry targeting, geopolitical developments, supply chain exposure, and regulatory pressure. The goal is to help decision-makers understand what is changing, why it matters, and what action the business should take.
To better understand this concept, we can distinguish three related terms:
Data is raw input, such as leaked credentials, malware logs, forum chatter, or domain records
Information is organized data with context, such as a report showing increased targeting of one sector
Intelligence is analyzed information that supports a decision, such as whether to increase investment in third-party risk controls or tighten identity protections
In short, data shows activity, while intelligence explains what that activity means for the business.
Strategic threat intelligence is built for an executive audience. It speaks to the board, the CISO, the risk committee, compliance leaders, and senior management. These stakeholders usually do not need deep technical detail. They need a clear view of major threat trends, industry-specific risks, likely business impact, and the trade-offs behind security decisions.
How strategic threat intelligence differs from operational and tactical intelligence
Threat intelligence is usually divided into tactical, operational, and strategic levels. Tactical threat intelligence helps security teams detect malicious activity, while operational threat intelligence lets analysts understand attacker campaigns and behavior. Strategic threat intelligence stands apart because it supports leadership decisions rather than day-to-day threat blocking.
While tactical and operational intelligence help security teams respond to attacks, strategic intelligence allows executives to understand long-term cyber risk and plan security investments. The difference is not just the audience. It is also the time horizon, the level of detail, and the kind of output each type produces.
Core components of strategic threat intelligence
Strategic threat intelligence works best when it follows a clear and repeatable process. The exact model varies by organization, but the core components tend to stay the same.
1. Define priority intelligence requirements (PIRs)
The first step is to define priority intelligence requirements, often called PIRs. These are the questions the intelligence function must answer to support business goals.
PIRs should connect directly to the company’s risk profile, growth plans, digital footprint, supply chain, and regulatory obligations. Without them, intelligence programs often collect too much data and produce too little value.
Executive-level PIRs often sound like this:
Which threat actors are most likely to target your organization this year?
Which parts of the business face the greatest ransomware exposure?
How could geopolitical tensions affect operations, partners, or data security?
Which third-party relationships create the highest cyber risk?
Which external signals suggest growing risk to the brand, credentials, or infrastructure?
A great strategic threat intelligence example is a CISO using these questions to shape quarterly reporting for the board and to justify investment in identity protection, vendor risk review, or external exposure monitoring.
2. Build an intelligence source strategy
Once PIRs are clear, the next step is to define the right intelligence sources. Strategic analysis is most effective when teams combine multiple inputs rather than rely on a single feed or vendor.
Useful sources often include:
Cyber threat intelligence (CTI) vendors
ISAOs and ISACs
Internal telemetry
Industry whitepapers and research reports
External breach and credential exposure data
Dark web, deep web, and Telegram monitoring
This matters because strategic assessments need context. A leaked credential dump means more when it matches broader attacker interest, sector targeting, or signs of rising ransomware activity. Pairing external sources with internal exposure data gives leadership a more realistic view of risk.
3. Profile threat actors
Strategic intelligence should identify which threat actors matter most, what drives them, and how capable they are. This step helps teams move from general awareness to predicting future risks.
Threat actor profiling usually evaluates:
Motivation, such as financial gain, espionage, disruption, or influence
Typical targets by sector or region
Known capabilities and preferred methods
Links to current campaigns or emerging tactics
This way, leaders can predict where future attacks may come from and what kinds of defenses deserve more focus.
4. Assess geopolitical and industry risks
Cyber risk does not exist on its own. Regional conflict, economic pressure, sanctions, new laws, and sector-specific attack trends all change how risk should be measured.
Strategic threat intelligence should account for:
Regional instability and spillover risk
Sector targeting patterns
New requirements tied to privacy, resilience, and reporting
The effect of regulations such as GDPR on risk management and disclosure
For many organizations, this is where intelligence moves beyond the security team. Legal, compliance, procurement, and executive leadership all need this context, too
5. Analyze business impact
Threat analysis is only half the story. Leadership needs to understand what a likely cyber event would mean in financial, operational, legal, and reputational terms.
This step should estimate potential consequences, such as:
Downtime and service disruption
Revenue loss
Regulatory scrutiny
Third-party fallout
Brand damage
Recovery costs
This turns threat intelligence into a decision-making tool rather than a list of observations.
6. Track emerging technology trends
A strategic program should monitor changes in attacker methods and underground markets. Examples include AI-driven phishing, credential theft at scale, infostealer activity, and ransomware as a service.
Monitoring ransomware statistics or threat research helps understand whether current controls match the threat environment.
7. Deliver clear reporting
The final step is reporting. Strategic intelligence only works if stakeholders can act on it.
Good reporting should be:
Concise
Decision-focused
Tied to business risk rather than technical data
Regular enough to support planning
Clear about how certain the assessment is, what assumptions it relies on, and what actions stakeholders should take
For leadership, the best output is usually an executive briefing, quarterly risk summary, or focused memo tied to a major business issue such as a market expansion, supplier review, or budget cycle.
Benefits of strategic threat intelligence
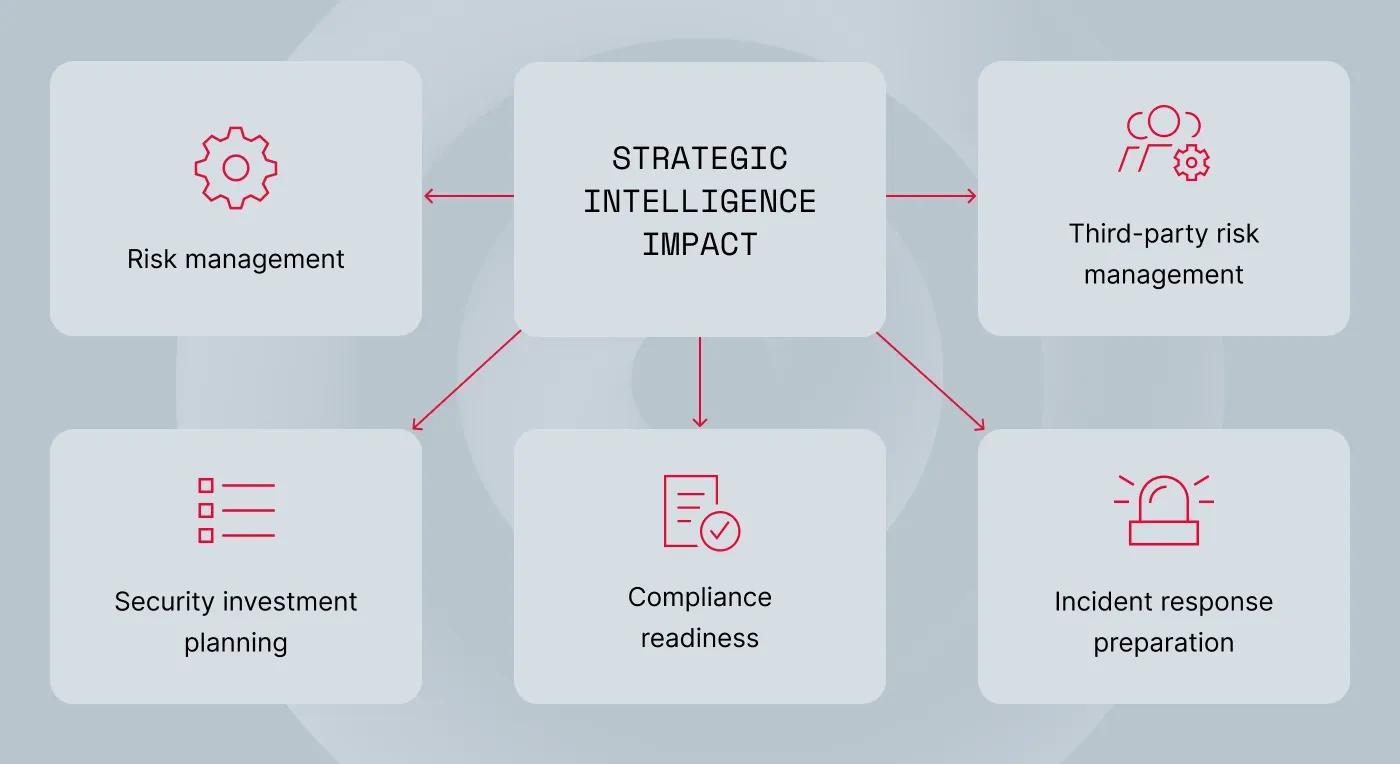
Strategic threat intelligence helps organizations move from reacting to threats toward anticipating and managing cyber risk more effectively. Instead of focusing only on technical alerts, it connects external threat developments with business priorities and security strategy.
For security leaders, this makes threat intelligence more than a monitoring function. It becomes a tool for planning, investment decisions, and cross-team risk management.
Stronger cybersecurity strategy
Teams can prioritize controls, investments, and long-term roadmaps based on likely threats rather than assumptions. By understanding which attackers target their sector and what techniques are becoming more common, security leaders can focus resources where they will have the greatest impact. This reduces wasted effort on low-probability risks and helps organizations build defenses that reflect the real threat landscape.
Better risk management and decision-making
Leadership gains a clearer view of which risks deserve attention, funding, and cross-functional planning. Instead of reacting to isolated incidents, executives can see broader patterns affecting their industry or region. This perspective helps organizations make more informed decisions about security investments, operational risk, and resilience planning.
Support for regulatory and compliance efforts
Strategic intelligence helps companies connect external exposure, threat trends, and reporting requirements with broader cybersecurity compliance work. Understanding how hackers exploit common weaknesses can guide improvements in identity management, data protection, or access controls that regulators increasingly expect. It also helps compliance and legal teams anticipate regulatory pressure rather than responding to it after an incident.
More informed incident response planning
Threat intelligence enables teams to prepare for realistic attack scenarios before incidents occur. By analyzing common tactics used by hackers targeting their sector, organizations can simulate likely attack paths and identify gaps in response capabilities. This preparation improves coordination between security, IT, and leadership when a real incident happens.
Better third-party risk evaluation
Modern organizations rely heavily on suppliers, partners, and service providers, which expands their potential attack surface. Strategic threat intelligence lets security teams understand how vulnerabilities in external ecosystems could affect their business. Monitoring breach activity, trends targeting a specific sector, and external exposure signals allow organizations to make better decisions about vendor selection, monitoring, and risk mitigation.
Related articles

Violeta LyskoitJan 19, 202510 min read

Aistė MedinėSep 9, 20258 min read
Challenges of strategic threat intelligence
Despite its value, building an effective strategic threat intelligence program is not always straightforward. Even mature security teams face obstacles that can limit the quality and usefulness of their analysis.
Understanding these challenges is key to designing intelligence programs that remain focused, practical, and sustainable.
Information overload
The cybersecurity ecosystem produces a massive amount of raw data every day, including threat feeds, breach reports, research publications, and underground activity. Without clear intelligence priorities, analysts may spend more time collecting information than producing insights that support decisions.
Data accuracy
Not all intelligence sources are reliable. Some information may be outdated, duplicated, or missing important context. Analysts must validate and correlate sources to avoid incorrect conclusions or overstated risk assessments.
Resource limits
Strategic threat intelligence requires analysts who understand both technical threats and business impact. Many organizations struggle to find time for this work because teams are already focused on operational security tasks and producing tactical threat intelligence for daily defense.
Too much focus on tactical data
Security programs often prioritize immediate detection and response, which means tactical data, such as indicators of compromise, can dominate reporting. While useful for SOC teams, this information rarely provides the broader insights leadership needs.
Changing threats
Threat actors, tools, and underground markets evolve quickly. New techniques, malware variants, and criminal partnerships appear constantly, making it difficult to rely on static assumptions about future attacks.
Despite these challenges, organizations that invest in strategic threat intelligence gain a more structured and forward-looking view of cyber risk, helping security leaders anticipate threats instead of constantly reacting.
How to build an effective strategic threat intelligence program
Organizations get the best results when their intelligence program stays practical and aligned with business needs.
Start with business risk priorities. If intelligence does not answer a real business question, leadership will struggle to see its value.
Define clear intelligence requirements. Good PIRs keep reporting focused and useful.
Build relationships across security, risk, legal, compliance, procurement, and IT. Strategic intelligence works best when multiple teams contribute context.
Use structured analytic techniques. These reduce bias and help teams separate assumptions from evidence.
Keep reporting concise. Senior leaders need clarity, not volume.
Review and update intelligence requirements regularly. Business priorities change, and intelligence should change with them.
Use suitable tools. A strategic program needs visibility into external risk, leaked data, brand abuse, exposed assets, and criminal ecosystem signals.
Threat exposure management platforms like NordStellar can help.
NordStellar supports strategic threat intelligence with dark web and Telegram monitoring, Data Breach Monitoring, attack surface management, and Domain Squatting Detection. That gives teams a clearer view of leaked credentials, exposed assets, suspicious domains, and external signals tied to business risk.
Try NordStellar to monitor leaked data, exposed assets, suspicious domains, and dark web activity that may affect your organization. Request a free trial to see how external risk monitoring can support strategic security planning.

Agnė Srėbaliūtė
Senior Creative Copywriter
Agne is a writer with over 15 years of experience in PR, SEO, and creative writing. With a love for playing with words and meanings, she crafts content that’s clear and distinctive. Agne balances her passion for language and tech with hiking adventures in nature—a space that recharges her.